By Brian Evans
Network-Centric Warfare derives its power from the strong networking of a well-informed but geographically dispersed force. – VADM Arthur Cebrowski, Proceedings 1998
Almost twenty years ago the pages of Proceedings carried an article by RDML Cebrowski that introduced the concept of network-centric, or net-centric, warfare.[1] The concept transformed the manner in which the United States (U.S.) Navy operates and fights. The principles that defined net-centric warfare remain relevant as they support Navy’s current pillars of Information Dominance: Battlespace Awareness, Assured Command and Control (C2), and Integrated Fires. The success of net-centric warfare has not gone unnoticed. Navies around the world are working to develop their own net-centric solutions. As a result, the U.S. Navy should not be surprised when enterprising individuals around the world similarly take note and make the evolutionary leap from traditional piracy to net-centric piracy.
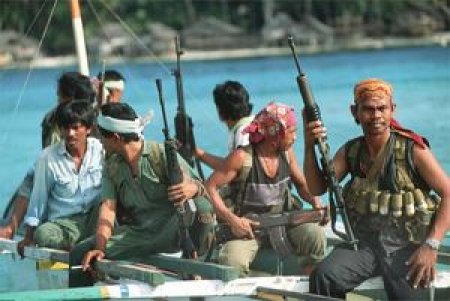
While piracy has been a scourge for the duration of human history, the technological advances of the 21st century provide potential pirates transformational means, methods and opportunities. While the world has yet to witness a case of net-centric piracy, the two scenarios below present possible piracy events leveraging today’s technology.
Basic Net-centric Piracy
Sixty-two nautical miles south east of Singapore – 17JUL15 1154C: An Indonesian pirate opens his laptop and logs onto the internet via satellite phone. His homepage is a commercial Automated Identification System (AIS) website providing real-time track data from coastal and satellite receivers.[2] The laptop, satellite phone and website subscription were all funded by his investors.[3] As he scans his homepage, he looks for AIS contacts that meet his desired vessel profile for cargo type, transportation firm, flag, and speed of advance. Today there are two AIS tracks of interest matching his profile and likely to pass through his preferred zone of operation, MV OCEAN HORIZONS and MW ORIENTAL DAWN. He then checks weather conditions and determining that they are favorable, he sends individual texts messages containing coordinate and track data for the AIS tracks of interest. The text recipients are two fishing boat captains, one located in Belawan, Indonesia and the other in Dungun, Malaysia.
Forty-six nautical miles east of Belwan, Indonesia – 17JUL15 1646C: MV ORIENTAL DAWN passes a non-descript fishing boat 46 nautical miles off the coast of Indonesia. Unbeknownst to the crew of the MV ORIENTAL DAWN, this fishing boat is captained by the pirate’s associate from Belawan. The fishing boat’s captain discretely observes the passing vessel through a pair of high-powered binoculars. Seeing barbed wire along the railings and an individual on the ship’s deck that does not appear to be a member of the crew, the fishing boat captain utilizes a satellite phone to call and report his observations to his Indonesian pirate contact. Based on this information the Indonesian pirate determines that MV ORIENTAL DAWN is not a suitable target.
One-hundred seventeen nautical miles east of Singapore – 17JUL15 1707C: The Indonesian pirate receives a call. This time it is the fishing boat captain from Dungun. The captain reports that the MV OCEAN HORIZONS is loaded down creating a smaller freeboard and there does not appear to be any additional security measures present. Given this assessment, the Indonesian pirate decides that MV OCEAN HORIZONS is a target of opportunity. He immediately has the crew of his ship alter course.
Thirty-seven nautical miles east of Pekan, Malaysia – 18JUL15 0412C: The Indonesian pirate launches two high-speed skiffs from his ship, both carrying multiple armed personnel. The Indonesian pirate mothership remains over the horizon, but in radio contact while the skiffs conduct the remainder of the intercept.
Sixty-two nautical miles east of Pekan, Malaysia – 18JUL15 0642C: The armed personnel from the skiffs board MV OCEAN HORIZONS and catch the crew off guard. Once in control of the ship, they contact the Indonesian pirate via radio and report their success. The Indonesian pirate immediately opens his laptop and reports his success to his investors. He also lists the ship’s cargo for auction on a dark website and sends a ransom demand to the employer of the MV OCEAN HORIZON crew.
Sophisticated Net-centric Piracy
Moscow, Russia – 17JUL15 0126D: After a series of all-nighters over the last week, a Russian hacker has gained access to a crewmember’s computer onboard the MV PACIFIC TREADER.[4] Using this access he maps the shipboard network. Discovering a diagnostic and maintenance laptop used for the ship’s automation and control system on the network, he quickly exploits the laptop’s outdated and unpatched operating system to install a tool on the automation and control system.[5] The tool enables a remote user to either trigger or disable a continual reboot condition. Once installed, the hacker posts the access information for the tool’s front end user interface in a private dark web chatroom.
Prague, Czech Republic – 16JUL15 2348A: Sitting in his Prague apartment, a pirate receives a message on his cellphone via a private dark web chatroom. The message is from one of several hackers he contracted to gain access to control or navigation systems onboard vessels operated by the TRANS-PACIFIC SHIPPING LINE. With the posted access information, he logs onto his laptop and tests his access into the MV PACIFIC TREADER automation and control system. After successfully establishing a connection he closes out of the tool and electronically transfers half of a contracted payment due to his hired hacker. Next using a commercial AIS website providing real-time track data from coastal and satellite receivers, he determines that MV PACIFIC TREADER is likely headed into port in Hong Kong.[6] Posting a message in a different private dark web chatroom, the pirate provides the identifying information for MV PACIFIC TREADER.
Hong Kong, China – 19JUL15 0306H: On a rooftop in Hong Kong, a young college student pulls an aerial drone out of her backpack. She bought it online and it is reportedly one of the quietest drones on the market. She also pulls three box-shaped objects out of her backpack. Hooking one of the objects to the drone, she launches it and flies it across Hong Kong harbor in the direction of a ship she identified during the day as the MV PACIFIC TREADER. Using the cover of darkness she lands the drone on the top of the pilot house and releases the object. Repeating this process twice more, she places the box shaped objects on other inconspicuous locations on the ship. After bagging up her drone, she posts a message to a dark web chatroom simply stating that her task is complete. Almost immediately afterwards she receives a notification that a deposit was made into her online bank account.
Prague, Czech Republic – 25JUL15 1732A: After eating a home-cooked meal, the pirate sits down at his laptop and checks the position of MV PACIFIC TREADER via the commercial AIS website he subscribes to. Observing that the MV PACIFIC TREADER is relatively isolated in the middle of the Pacific Ocean, he opens the remote tool that provides him access to the ship’s automation and control system. He sends a text message and then clicks to activate the tool.
Two-thousand ninety-three nautical miles north east of Hong Kong – 26JUL15 0332K: Onboard MV PACIFIC TREADER an explosion engulfs the bow of the ships sending flames into the dark air. Immediately, the ship’s engines roll to a stop as the navigation and ship’s control system computers go into a reboot cycle. The lone watchstander on the bridge is paralyzed to inaction by the surprise and violence of the events unfolding around him. The Master immediately comes to the bridge, completely confused by the events occurring onboard his ship.
Prague, Czech Republic – 25JUL15 1736A: The pirate confirms via his remote tool that the ship’s automation and control system is in a continuous reboot cycle, then he re-checks the commercial AIS website and confirms that MV PACIFIC TREADER is dead in the water. He immediately sends an email to the TRANS-PACIFIC SHIPPING LINE demanding a ransom, stating MV PACIFIC TREADER will remain dead in the water and more explosive devices will be activated until he is paid.
New Means – Same Motive
These scenarios illustrate how the evolution of technology and the increased connectivity of systems and people potentially enable a fundamental shift in the nature of piracy. Despite the change in means and geographic distribution of actors, net-centric and traditional piracy both utilize physical force or violence, or the threat thereof, by a non-state actor to seize or detain a vessel operating on the high seas. The key enabler of net-centric piracy is the Internet.
The Internet is the net-centric pirate’s “high-performance information grid that provides a backplane for computing and communications.”[7] Admiral Cebrowski argued that this information grid was the entry fee for those seeking net-centric capabilities.[8] What Admiral Cebrowski did not know was how rapidly the Internet would evolve and enable near-instantaneous global communications at relatively low costs, allowing anyone who desires access to a high-performance information grid.
As the net-centric pirate’s high-performance information grid, the Internet serves as a command and control network as well as the means for disseminating intelligence information, such as vessel location or the presence of physical security measures. The intelligence that is disseminated may also have resulted from collections performed via the Internet. One collection means is to leverage the vast area of private and commercial data sources available for public consumption, again at little or no cost, such as shipping schedules and AIS data. A second means of collection uses the Internet to conduct intelligence, surveillance and reconnaissance (ISR) via cyber techniques; however, only the most sophisticated net-centric pirates will possess this capability. Similarly, highly sophisticated net-centric pirates may be able to achieve global weapons reach by producing physical effects via cyber means over the Internet, eliminating the need for the pirate to be physically present in order to seize or detain a vessel.

The attractiveness of net-centric piracy is the low barrier to entry, both in risk and cost. Since the Internet is the key enabler of net-centric piracy, its low cost and ease of use vastly expand the potential pirate population. The anonymity of the Internet also allows potential net-centric pirates to meet, organize, coordinate and transfer monetary funds with a great degree of anonymity. As a result, the risks of arrest or capture are significantly reduced, especially since a net-centric pirate may not be able to identify any of their co-conspirators. Similarly, the ability of net-centric piracy to enable remote intelligence gathering or even produce physical effects via cyber techniques removes a significant element of physical risk associated with traditional piracy. The monetary gain from the successful capture of a vessel compared to the low cost and risk currently associated with net-centric piracy make it an attractive criminal enterprise.
Countering Net-centric Piracy
The United Nations Convention of the Law of the Sea (UNCLOS) Article 101 defines piracy as:
- any illegal acts of violence or detention, or any act of depredation, committed for private ends by the crew or the passengers of a private ship or a private aircraft, and directed:
- on the high seas, against another ship or aircraft, or against persons or property on board such ship or aircraft;
- against a ship, aircraft, persons or property in a place outside the jurisdiction of any State;
- any act of voluntary participation in the operation of a ship or of an aircraft with knowledge of facts making it a pirate ship or aircraft;
- any act of inciting or of intentionally facilitating an act described in subparagraph (1) or (2).[9]
Under this internationally recognized legal definition of piracy, net-centric piracy clearly results in violence against or detention of vessels on the high seas for private ends. It is also clear from this definition that any activities associated with facilitating a piracy event, such as intelligence collection or compromising a vessel’s computerized control systems, are also considered piracy under international law. International law also states that “All States shall cooperate to the fullest possible extent in the repression of piracy on the high seas or in any other place outside the jurisdiction of any State.”[10] As a result, the international community must resolve how it will counter net-centric piracy, where pirates need not operate on the high seas and may be located thousands of miles from the target vessel.
The challenge facing the international community from net-centric piracy is compounded by immaturity of international cyber law. Currently the authorities and responsibilities of international organizations, governments and law enforcement agencies with regards to the use of the Internet to commit piracy are undetermined. This challenge is further complicated by the fact that the Internet is a manmade domain where all potions are essentially within the territory of one state or another. As a result, disrupting net-centric piracy operations will require a significant degree of international coordination and information sharing. Extensive international cooperation will also be required to identify, locate, and apprehend individuals involved in net-centric piracy.

While an occurrence of net-centric piracy has yet to occur, the opportunity and capabilities required for such an event exist today. The U.S. Navy should not be caught off guard. Instead, the Navy should take the following actions:
- Raise awareness within the international maritime community regarding the risks and realities of net-centric piracy
- Provide best practice and limited cybersecurity threat information to transnational maritime shipping companies
- Work with partner Navies to develop means and methods for disrupting net-centric piracy, including developing an appropriate framework for information sharing and coordination
- Work with Coast Guard, law enforcement and international partners to develop a cooperative construct for identifying, locating and apprehending net-centric pirates
- Engage with the State Department to advance international dialog on net-centric piracy, including the need for consensus on international law and processes for prosecution of net-centric pirates
An enduring lesson of human history is that opportunity for profit, regardless of difficulty or brevity, will be exploited by someone somewhere. Net-centric piracy represents an opportunity to generate revenue without requiring the physical risks of traditional piracy. The anonymity and distributed nature of the cyber domain also creates new counter-piracy challenges. Add to this the low cost and availability of unmanned system components coupled with the low barrier of entry for cyber, and the question becomes not whether net-centric piracy will occur but when. With a global interest in maintaining the international maritime order and ensuring the uninterrupted flow of commerce on the high seas, the U.S. Navy must be ready to meet the challenges of net-centric piracy.
LCDR Brian Evans is a U.S. Navy Information Dominance Warfare Officer, a member of the Information Professional community, and a former Submarine Officer. He is a graduate of the U.S. Naval Academy and holds advanced degrees from Johns Hopkins University, Carnegie Mellon University, and the Naval War College.
The views expressed in this article are those of the author and do not reflect the official policy or position of the United States Navy, Department of Defense or Government.
[1] VADM Arthur K. Cebrowski and John H. Garstka, “Network-Centric Warfare – Its Origin and Future,” U.S. Naval Institute Proceedings, Volume 124/1/1,139 (January 1998).
[2]https://www.vesseltracker.com/en/ProductDetails.html
[3] “Somali Piracy: More sophisticated than you thought,” The Economist (November 2nd, 2013), http://www.economist.com/news/middle-east-and-africa/21588942-new-study-reveals-how-somali-piracy-financed-more-sophisticated-you
[4] Jeremy Wagstaff, “All at sea: global shipping fleet exposed to hacking threat,” Reuters (April 23rd, 2014), http://www.reuters.com/article/2014/04/24/us-cybersecurity-shipping-idUSBREA3M20820140424
[5] Mate J. Csorba, Nicolai Husteli and Stig O. Johnsen, “Securing Your Control Systems,” U.S. Coast Guard Journal of Safety & Security at Sea: Proceedings of the Marine Safety & Security Council, Volume 71 Number 4 (Winter 2014-2015).
[6]https://www.vesseltracker.com/en/ProductDetails.html
[7] VADM Arthur K. Cebrowski and John H. Garstka, “Network-Centric Warfare – Its Origin and Future,” U.S. Naval Institute Proceedings, Volume 124/1/1,139 (January 1998).
[8] Ibid.
[9] United Nations, United Nations Convention on the Law of the Sea (New York: United Nations, Article 101, 1994).
[10] United Nations, United Nations Convention on the Law of the Sea (New York: United Nations, Article 100, 1994).