Gordon, Andrew. The Rules of the Game: Jutland and British Naval Command. Annapolis: Naval Institute Press, 2013, reprint ed. 708pp. $34.95
By Captain Dale Rielage
There is always interest, and usually value, in reading what the boss is reading. Since General Al Gray established the Marine Corps reading list in the late 1980s, reading lists have proliferated across the military services. The Marine Corps Library website lists more than twenty. While the original Marine Corps reading list bore General Gray’s own unique stamp, today most military reading lists feel like the product of a committee – because most are – developed with an eye towards representing every facet and constituency in their institution. What has personally informed and moved a thoughtful warrior, however, is more interesting than the consensus of any committee…which is why, for example, Admiral Stavridis’s reading recommendations are always worth taking aboard. Earlier this month, one of my colleagues made reference to the classic work The Rules of the Game. His comment sent me back to my bookshelf. There, in the recent Naval Institute reprint edition, I noticed an epigraph that escaped my attention years ago:
This edition has been brought to publication with the generous assistance of VADM John M. Richardson, USN, Commander, Submarine Force, and VADM Peter H. Daly, USN (ret.) CEO, US Naval Institute, in the interest of helping put this book in the hands of current and future naval professionals.
It is one thing for a book to make an official reading list, but when the (then) future Chief of Naval Operations is willing to help a book to remain in print, it bears a second look. What any particular senior officer saw in this volume I can only speculate, but a couple lost weekends later, it is clear that Rules of the Game speaks to the most profound challenges facing the U.S. Navy.
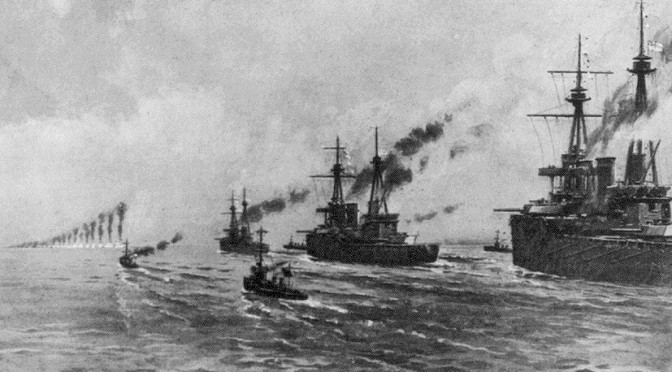
On the surface, a 600-plus page (708 pages with notes and appendixes) book about the Battle of Jutland seems an unlikely means to examine the established order of U.S. Navy command and control. The fight between the British Royal Navy and the German High Sea Fleet in the North Sea on 31 May and 1 June 1916 was the largest naval battle of World War I. This epic clash of dreadnought battleships is widely regarded as a draw, with neither side achieving clear victory. Gordon, however, turns the Royal Navy at Jutland into a long case study of the role of doctrine, training, centralization, initiative, and institutions in naval warfare. He begins his analysis as the fleet engagement at Jutland is starting, with the Battle Fleet and the Battle Cruiser Fleet, the two key combat formations that comprised the Royal Navy’s Grand Fleet, getting underway from their respective homeports 200 miles from each other. So good was British naval intelligence in this era that the Grand Fleet weighed anchor in response to a planned German sortie more than four hours before the German High Sea Fleet reached the open sea.
As the narrative arrives at the moment enemy forces are in contact and key tactical decisions are being made, Gordon shifts his view back a century. In a 200 page excursion, he introduces the competing naval schools of thought and the resulting institutional habits and personal relationships that led to the British fleet acting as it did at Jutland.
Britain left the Napoleonic Wars with a navy second to none and a tradition of victory built on the aligned independence of Nelson’s band of brothers. Nelson’s famous flag hoist opening Trafalgar was the last he made during that battle – not because of his death, but because he needed no other. Shortly after the war, however, new visual signaling systems promised increasing control over the movements of forces in combat. In peacetime drills, these systems yielded reliable execution of complex maneuvers. However, the reality of how this signals system would work in combat was lost over decades. In the breach, smoke from engineering and gunnery, signal masts and halyards destroyed by gunfire, signalmen lost to shot and shell, and the sheer volume of communications in a fleet engagement would conspire to negate centralized command and control. The promise of centralized control and effective coordinated combat action, however, produced a deep influence on the Royal Navy.
In what Gordon memorably dubbed “the long lee of Trafalgar,” the Royal Navy continued to dominate the seas. Its officers retained the expectation of victory bequeathed them by their predecessors. That there had been no major fleet action in living memory was discussed, but rarely with concern. The French or Russian navies occasionally caused alarm, but no “peer competitor” called into question the fundamentals of the system – the rules of the game.
There was good reason for this comfort. By almost every metric, the Royal Navy in the second half of the nineteenth century was extraordinarily successful. Its officers were masters of seamanship and navigation and created the standard for contemporary and modern navies. Operating forward in defense of a worldwide empire, many Royal Navy officers had seen combat and had demonstrated personal courage and resourcefulness. Beatty, commander of the Battle Cruiser Fleet at Jutland, had earned distinction – and favorably impressed a young Winston Churchill – in littoral action using river gunboats to support ground forces in Egypt. Work to understand and incorporate new technologies proceeded apace, with a limited cadre of specialists articulating the new technology to the fleet at large. There were efforts to change operational culture, most prominently spearheaded by the driven and charismatic Admiral Sir George Tyron. Tyron advocated a looser form of control, emphasizing formations following the Commander’s intent as understood or expressed in the movements of his flagship. His untimely death in a collision at sea – ironically and unfairly blamed on his style of signaling – arrested reform efforts for decades.
Having allowed the German Fleet to avoid decisive battle and escape home, the Royal Navy left the field at Jutland with a sense of failure that grew as the war concluded. Denied the decisive fleet action they expected, senior British commanders engaged in decades of controversy over what signals were sent, received, intended, and expected. This controversy colors any discussion of the battle to this day. Gordon, however, seeks to move this discussion to a more profound level. While individual commanders executed the action at Jutland, their failure to exercise initiative at key moments was not truly an individual act. Indeed, Gordon asserts that the sudden exercise of tactical initiative would have been an unnatural rejection of the culture that had nurtured them through their entire professional lives.
In his final chapter, Gordon draws twenty-eight specific observations from the Jutland experience. They are directed toward the Royal Navy of the early 1990s, but will resonate with serving officers today. Gordon rails against command and control being driven by the tools of information processing. Absent deliberate restraint, every increase in the capacity to transmit information produces an increase in the amount of information transmitted – with the capacity of the senior to send information, rather than the capacity of the junior to assimilate information, driving the flow. The focus too easily becomes getting the mechanisms of communications right, believing that with that information dominance achieved, success in command and control ensues. Ready access to information and the ability to transmit orders raises the level of decision making further from the point of action. When these links fail – today from jamming, cyber attack, or destruction of communications satellites – it is folly to expect naval commanders in combat will suddenly be able to shed the culture in which they have been trained.
Gordon also highlights the difficulty of integrating new concepts and technologies into a peacetime navy. In the Royal Navy of 1900, enthusiasts for new technologies drove the stated purpose and design of new weapons – much like our navy today. Their specialized focus ignored or obscured real operational challenges to their systems. Once a new system or platform arrived in the Fleet, however, its integration and employment became the business of fleet officers who were and are often working from different approaches than the cadre of experts who designed it. As practical naval officers, they rarely set a capability aside as too flawed for use, but rather would often “make the best of it,” sometimes using the ship for an entirely different purpose than intended. At Jutland, the Royal Navy Battle Cruiser Fleet consisted of ships designed to mount heavy guns but limited armor. Their superior speed was intended to allow them to manage their range to more heavily protected enemies. In actual combat, managing this thin envelope of safety proved too difficult. 3,300 British sailors died in these ships – ten percent of all the British sailors who participated in the battle – in what Gordon aptly calls “a costly rediscovery of the designer’s terms of reference.”
That insight brings us to Gordon’s overarching theme – how the Royal Navy dealt with a long peace, technological change, and an emerging German challenge to its comfortable dominance of the maritime domain. It is a short leap to ask to what extent the U.S. Navy remains, to paraphrase, in the long lee of Midway. It is a question the service must be comfortable asking, whether or not the answers are comfortable.
Aside from its impact and insight, The Rules of the Game is delightfully written. Gordon has a knack for memorable turns of phrase and admirable clarity (if not economy) of expression that makes the long journey through his thinking as enjoyable as it is intriguing. Every naval professional’s bookshelf should have a well-thumbed copy of this volume.
Captain Rielage serves as Director for Intelligence and Information Operations for U.S. Pacific Fleet, the headquarters where the Midway operation was commanded and controlled. He has served as 3rd Fleet N2, 7th Fleet Deputy N2, Senior Intelligence Officer for China at the Office of Naval Intelligence and Director of the Navy Asia Pacific Advisory Group. His opinions do not represent those of the U.S. Government, Department of Defense, or Department of the Navy.
Twenty-Eight Observations from The Rules of the Game
by Andrew Gordon
Lessons from the Battle of Jutland
31 May to 1 June 1916
1) In times of peace, empirical experience fades and rationalist theory takes its place.
2) The advent of new technology assists the discrediting of empirical doctrine.
3) The purveyors of new technology will be the most evangelizing rationalists.
4) Rationalism, unlike empiricism, tends to assume an accretion of vested interests.
5) The training establishment may try to ignore short bouts of empirical experience to preserve its ‘rationalist’ authority.
6) Military cultures impart doctrine by corporate ambience as much as by explicit teaching.
7) In long periods of peace, ‘ambient’ doctrine may be no more than the habits of years in which war has been forgotten.
8) If doctrine is not explicitly taught, vested interests will probably ensure that wrong doctrine is ambiently learned.
9) In peacetime, doctrine is vulnerable to commandeering by ‘systems lobbyists.’
10) Innovations adopted in accordance with peacetime doctrine may lock the Fleet into both systems and doctrine which will fail the empirical test of war.
11) Purveyors of technical systems will seek to define performance criteria and trials conditions.
12) A service which neglects to foster a conceptual grasp of specialized subjects will have too few warriors able to interrogate the specialists.
13) The volume of traffic expands to meet capacity.
14) Signals ‘capacity’ tends to be defined by how much the senior end can transmit rather than how much the junior end can conveniently assimilate.
15) Signal prioritizing mechanisms become dislocated in times of overload.
16) Incoming traffic can act as a brake on decision-making.
17) The more signals, the more the sun shines on signalers.
18) The ‘center’ must subject its own transmissions to the strictest self-denying ordinance.
19) Signaling promotes the centralization of authority.
20) There is an inverse law between robust doctrine and the need for signaling.
21) Heavy signaling, like copious orders, is symptomatic of doctrinal deficiency.
22) The promise of signaling fosters a neglect of doctrine.
23) War-fighting commanders may find themselves bereft of communications faculties on which they have become reliant in peacetime training.
24) Properly disseminated doctrine offers both the cheapest and the most secure command-and-control method yet devised by man.
25) Every proven military incompetent has previously displayed attributes which his superiors rewarded.
26) Peacetime highlights basic ‘primary’ skills to the neglect of more advanced, more lateral ‘secondary’ abilities, the former being easier to teach, easier to measure, and more agreeable to superiors.
27) The key to efficiency lies in the correct balance between organization and method.
28) Doctrine draws on the lessons of history.