By Ian Akisoglu
Since the end of the Second World War, the military dominance of the United States has rested on its relative technological superiority over its adversaries, what has been underwritten by its impressive economic strength and high-tech domestic industries. For the first time in seventy years, the United States military is forced to contemplate a long-term strategy without the implicit guarantee that it will enjoy decisive technological superiority as its most likely adversaries come closer and closer to achieving parity in both technological and economic strength. In order to remain viable in future conflicts, the American military will have to rethink its operational paradigm and learn to rely more heavily on the creativity and individual zeal of its leaders and less on its hard assets.
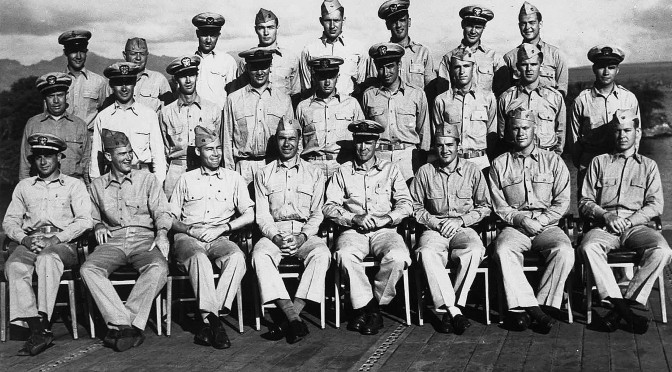
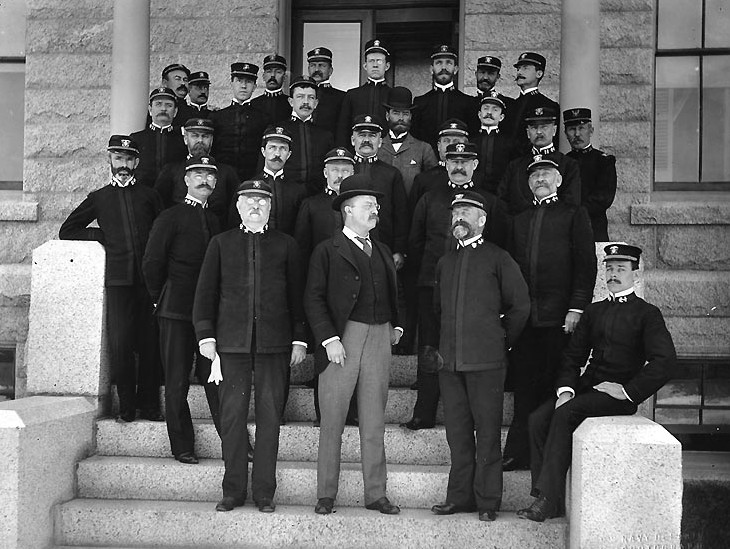
For much of its history, the American military has fought its major conflicts without the overwhelming technological and financial superiority that it has enjoyed since the end of the Second World War. I believe that this phenomenon can best be explained by the following paradigm: raised in an age where American military power was relatively lacking on the world stage, the American officer corps did not possess any of the bad habits or laziness of thought engendered in today’s officer corps. Looking down on the rest of the world’s militaries from a plateau of overwhelming superiority and relative security, we have become haughty and ignorant of our peers’ capabilities. Previously generations of American military officers were forced to contend with a world in which the United States Army and Navy were not the best – indeed, not even in the top ten at times.
This forced American military leaders to develop and utilize a currently unimaginable level of organizational, operational, and strategic creativity comparably unknown to the armed forces of today, where an over-reliance on financial superiority has led to an over-reliance on technological superiority, which has led to an over-reliance on established procedures and doctrine. In order for the armed forces of the United States of America to continue to enjoy success in the future, both on the battlefield and as a viable instrument of soft power, American military leaders must look to lessons from the past and re-learn how to plan and fight wars without the assumption that they will always enjoy superiority of force.
[otw_shortcode_button href=”https://cimsec.org/buying-cimsec-war-bonds/18115″ size=”medium” icon_position=”right” shape=”round” color_class=”otw-blue”]Donate to CIMSEC![/otw_shortcode_button]
A humorous quote from a European officer highlights the benefit of this, “One of the serious problems in planning against American doctrine is that the Americans do not read their manuals nor do they feel any obligations to follow their doctrine.” This emphasizes the extensive freedom of judgment American commanders previously enjoyed while executing missions in complex operational environments. From the author’s perspective as a contemporary unrestricted line officer in the U.S. Navy, this freedom of judgment is virtually non-existent nowadays. Instead, American military commanders are so hamstrung by strict adherence to the protocol and procedures that have been enshrined throughout their military upbringings that they are often afraid to rely on their own intuition, experience, and creativity. This risk aversion is not unjustified since the risk to reward ratio for officers willing to try new ideas has shifted so heavily to the risk side, that many deem the potential gains not worth imperiling their careers over. The main problem with this method of doing business is that operational arenas are not the static playing fields that we presuppose them to be in most exercise and operation briefs. They are constantly evolving, which requires adaptability and ingenuity instead of a flow-chart approach to missions.

This is not meant to be a rebuke of procedural compliance – far from it. Procedural compliance is important to ensure the safety and proper execution of our technical missions: safety and maintenance. However, it is important to also recognize its inherent limitations, and understand that it’s impossible to write “winning a war” into procedural compliance, since procedures only extend to the realm of what is known, and war often devolves into the area of the unknown. Simply put, officers should be proficient at procedural compliance and planned execution, but once the situation is no longer covered by procedures, strategic entrepreneurship and improvisation must take over seamlessly. If we consistently deny our Navy leadership the ability to improvise and test their creative problem solving abilities for fear of imperiling their careers, how and when can this creative solution seeking process be fostered?
The key question then is how do we recapture the ingenuity of the individual officer? I assert that it must start at the earliest possible point in the officer’s career – for creativity once lost is nearly impossible to rediscover. The Navy should develop programs that both encourage and train officers to think of creative solutions to problems early on in their careers. The best time to start this is at the O-2 and O-3 levels, directly after the completion of an officer’s initial warfare qualifications and first operational tour.
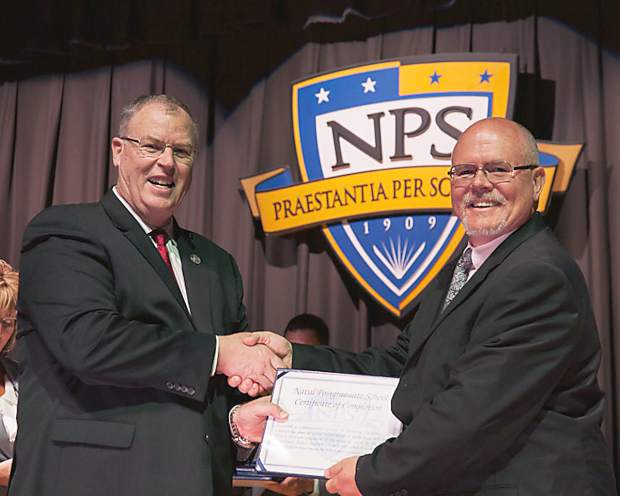
The importance of instilling and encouraging the idea of creative thought early on in the officer corps cannot be overstated. Senior officers that attend the Naval War College relatively late in their careers to explore ideas on war and its strategic theory have already come to depend on the rigidity of the Navy establishment for their paychecks and lifestyle, and thus are less willing to question the institution or its authority. The junior officer, relatively fresh and with fewer mental harangues, owes no such allegiance to the organization and does not see it through the same cynical lens, allowing them to see the flaws in our organization much more clearly than a dyed-in-the-wool career officer. These junior officers are still willing to question the military’s fatal deficiencies and flaws before becoming completely indoctrinated into the system.
One way to implement this would be to establish a school that officers attend with peers from their warfare areas concentrated around every major career milestone. The goal of such a school would be to gather high-flying officers into small groups where they would be posed complex operational problems. However, they would face them with handicaps and constraints put in place, making normal doctrine and pre-planned responses obsolete, and forcing them to develop creative solutions to real world problems. Officers would return to the course at every major career milestone, such as in between division officer tours, prior to starting their department head tours, prior to beginning their XO/CO fleet-up, and prior to achieving flag rank.
One of the most resonant lessons that has been gleaned from the attacks on the USS Stark, USS Samuel B. Roberts, and USS Cole is that in unexpected situations, conventional procedures often are inadequate, and improvisation dominates. Generations of American military officers have become complacent through the knowledge of their nation’s technological and financial superiority. It is time to train them to think and fight absent this implicit safety net once again. It is better to start learning these critical skills now, while remaining in control of the pace, than to be forced to learn them under fire in a future conflict.

Secondly, while an understanding of mathematics and the sciences remain ever important in an increasingly technical and specialized military, officer programs must also recapture the emphasis on liberal arts education and creative thinking that has steadily dwindled in the twentieth and twenty-first century formation of modern military officers. At the United States Naval Academy it is a requirement that sixty-five percent of those graduates must complete degrees in the science, technology, engineering, or mathematics disciplines. Of students commissioning from ROTC programs around the country – which, combined with the Naval Academy, contribute roughly two thirds of new officer accessions the fleet each year – eighty-five percent of available scholarships are rewarded to those students who choose majors in the STEM fields. Those remaining fifteen percent who do express interest in studying disciplines outside of these fields, ignominiously referred to as “Tier 3” majors, find their options for earning scholarships and commissioning more limited.
Technical courses do an excellent job training officers to operate complex combat systems and nuclear reactors, where every aspect can be distilled to checklists and procedures, but do a poor job in training strategic and creative thought. Such critical thinking skills are ultimately where officers render the greatest value to the armed forces as leaders and warfighters, not technicians. At a minimum, a certain number of liberal arts courses in subjects such as philosophy, history, literature, and economics should be required for certain officer programs in just the same way that calculus, physics, and other mathematics and science courses are. An officer able to harness the problem-solving ability taught by an education in engineering with the propensity for creative though that comes from a study of the liberal arts would be the best equipped to execute all of the Navy’s missions.
Thirdly, the United States military must push decision-making back down the chain of command to the unit level. In our age of global real-time communication we have achieved the ability to control even the minutest detail from the highest level. We must resist the temptation to do so, for this robs on-scene commanders of the crucial experience that comes from tense, independent decision-making. Instead, we must once again become comfortable with giving commanders autonomy over their units and operations, giving direction only in broad strokes and leaving the details to the “man on the spot,” who is inevitably the subject matter expert on what is happening within and directly around his unit. In today’s fleet, the number of daily updates that a deployed warship is required to provide up the chain of command off-ship has become a full-time job on top of the full-time job of running the ship and executing its mission. No effective leader has two full-time jobs.
And all of this for what? It is absolutely ludicrous to imagine that a remote commander and their staff, often years detached from single-unit leadership, require or need all of the information now required to be tracked on a daily basis. The massive off-ship administrative burden that this places on the wardroom of an operational unit, simultaneously interfering with their ability to effectively do their job within the lifelines of the ship, significantly degrades morale and unit-level success. By fostering a culture in which officers are afraid of making even the smallest decisions themselves, we are handicapping the abilities of junior officers to develop leadership skills and to learn to take the initiative, resulting in the ones who adapt to this climate being cautious to a fault for the rest of their careers, and inducing those individuals who want more control and autonomy to seek opportunities elsewhere.
Finally, the United States military must consider drawing talent into its ranks from untraditional sources outside the military and recognize that its rigid and traditional career path that exclusively emphasizes hiring and promotion from within might have to change. This is not entirely without precedent – the Navy already does this for many of its staff corps officers who have demonstrated experience and proficiency in their civilian careers. There are many individuals with different backgrounds and specialties who hear the call to serve their country at different points in their life. A master software engineer at Google with ten years in the industry would be an incredible asset to the military’s cyber warfare communities, but at that point in his career he would likely be too old to enlist and would have his talents wasted as a newly-commissioned ensign while also being grossly under-compensated. Instead, why not bring this cyber star in as a Lieutenant Commander? This arrangement would offer significant benefits and opportunities to both the military and the individual.
If the United States wants to avoid catastrophe on the battlefield in the coming decades, it will need to come to terms with the fact that having more money and better technology will no longer be enough to win the next war against the next foe – who may very well enjoy parity in these domains, if not even superiority. Accepting this, rather than continuing to do the same thing while expecting a different result, is a required preliminary step.
The United States military must fundamentally change the way it does business and drive its officer corps to rediscover skills that gave way to technology and money when they seemed to no longer be needed or valued. In order to do this, we must encourage creative thought in our officers starting at a very junior level – both by commissioning a greater portion of our officers with backgrounds in the liberal arts as well as technical majors, and by creating incubator programs at multiple levels of officer career tracks to cultivate and stimulate creative thought. The military must also learn to re-delegate greater amounts of control and authority to unit commanders while unit commanders must learn to do the same to their subordinates. This ensures that if subordinate commanders are fighting a conflict in which they are cut off from communication with headquarters or things are not going quite as they had expected them to, they aren’t paralyzed with indecision, experiencing what is in effect their first ever real experience with high-stakes decision making.
Finally, the United States must harness the huge pool of potential talent that exists in the form of civilians who want to serve but don’t fit into the current recruiting construct. By allowing experienced non-military personnel to enter the organization at mid and even upper-level officer positions, the military can harness a huge untapped reservoir of private sector talent. The same skills that our military forefathers used to achieve victory on the battlefield when outclassed in technology, money, manpower, and weapons – creativity, zeal, initiative, and guile – are needed once again. All that is lacking is the will and tenacity to bring them back.
Lieutenant Junior Grade Ian Akisoglu is a Surface Warfare Officer living in Norfolk, Virginia. He graduated from American University with a Bachelor of Arts in economics and history and was subsequently commissioned through Officer Candidate School. The views expressed here are his own and do not represent those of the U.S. Department of Defense or the Department of the Navy. He can be reached at ian.akisoglu@gmail.com.
[otw_shortcode_button href=”https://cimsec.org/buying-cimsec-war-bonds/18115″ size=”medium” icon_position=”right” shape=”round” color_class=”otw-blue”]Donate to CIMSEC![/otw_shortcode_button]
Bibliography:
Kimbrough IV, James M. MAJ, USA. (2008). Examining U.S. Irregular Warfare Doctrine. 14.
United States Naval Academy. (2015). Academics – Majors and Courses.
Population Representation in the Military Services FY 2013 Report: Appendix B: Active Component Enlisted Accessions, Enlisted Force, Officer Accessions, and Officer Corps Tables.
United States Navy ROTC. (2015). Naval Reserve Officers Training Corps Scholarship Selection Criteria.
Long, Roger D. The Man On The Spot: Essays on British Empire History. (Ed.), Praeger, First Edition (Sep 26, 1995).