Future Capital Ship Topic Week
By Zachary Kallenborn
“A ‘capital ship,’ rightly understood, is a ship type that can defeat any other ship type. In the days of sail and dreadnoughts, it was the type of ship having the most and biggest guns. It is the ship type around which fleet doctrine and fleet architecture are established. The question is what kind of killing weapon the capital ship supports.”
—Robert Rubel1
Introduction
The Navy’s Strategic Studies Group 35 concluded the “Navy’s next capital ship will not be a ship. It will be the Network of Humans and Machines, the Navy’s new center of gravity, embodying a superior source of combat power.”2
Such a network could consist of networks of sea mine swarms and their support ships. Networked sea mine swarms could converge on masses of adversary ships, bringing to bear overwhelming force. The visibility of surface support ships would enable the network to generate conventional deterrence by signaling the swarm’s presence, while helping maintain the swarm itself.3 The history of mine warfare suggests swarming sea mines could deliver a decisive force.
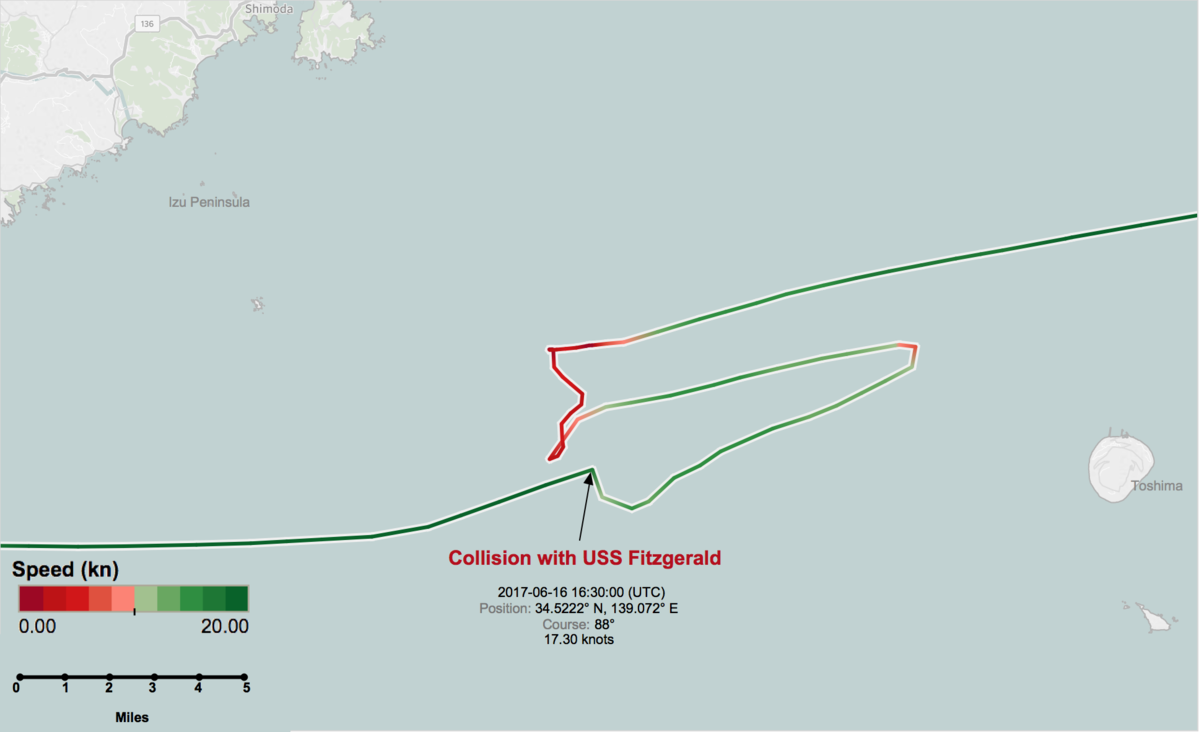
Sea mines can already inflict significant damage on all other types of ship, including capital ships.4 On April 14, 1988, a single contact mine nearly sank the USS Samuel B. Roberts (FFG 58), causing over $96 million in damage.5 Since World War II, mines have seriously damaged or sunk 15 U.S. ships, nearly four times more than all other threats combined.6 However, unlike aircraft carriers and other capital ships, traditional sea mines offer little ability to project power and, once identified, can be avoided.
But what if sea mines could move themselves intelligently and coordinate their actions? They could rove the seas in advance of friendly fleet movements and position themselves into an adversary’s path. Multiple mines could strike a single target. Naval mines could become a critical aspect of seapower. Networks of naval mine swarms could become the future capital ship.
Swarming sea mines can do exactly that.
Swarming Sea Mines: The Concept
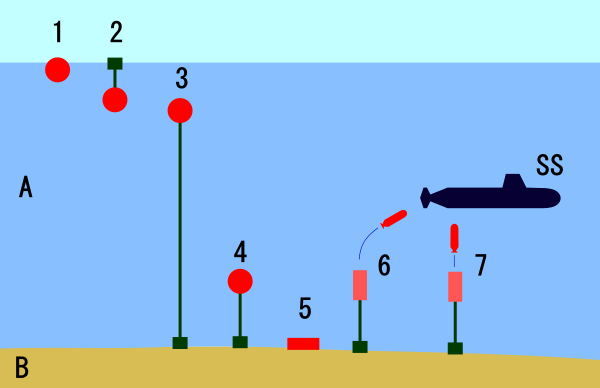
Swarming sea mines consist of interconnected, undersea drones dispersed over an area. Drones within the swarm communicate with one another to coordinate their actions. Sensor drones7 within the swarm disperse, broadly searching for incoming targets. Sensor drones relay information to attack drones to engage an adversary vessel, or stand down to allow a friendly vessel to pass.
Attack drones may be either undersea turrets or free-roaming munitions. As undersea turrets, attack drones serve as platforms for launching torpedoes or other munitions. Input from sensor drones informs the trajectory for launch. As a free-roaming munition, an attack drone functions like a traditional sea mine. Using on-board propulsion systems, the attack drone maneuvers to the adversary vessel and detonates in proximity.
Interconnectivity enables swarming attacks. Multiple attack drones may launch attacks from different directions. This increases the likelihood of successfully sinking an adversary ship because (1) strikes hit different parts of the adversary hull and (2) it enables multiple strikes on the same target, putting at risk larger ships that may survive a single detonation. Interconnectivity could also enable networks of sea mine swarms to coordinate strikes, significantly increasing the number of attack drones. Such a capability would be useful in attacking an adversary fleet, with multiple swarms coordinating target selection.
As the size of the swarm grows, so too does its combat power. Larger swarms mean more sensors in the network and more munitions to overwhelm targets. The Department of Defense (DoD) recently fielded a swarm of 103 aerial drones.8 China also reportedly fielded a swarm of 1,000 aerial drones.7 In theory, a sea mine swarm could consist of tens of thousands of interconnected mines, able to overwhelm any target. The primary limitation on swarm growth is the capacity to manage the rapidly increasing complexity of drone information exchange.
Strategically, swarming sea mines could play the same roles as traditional sea mines. Sea mines may be used to control critical chokepoints. During the Iran-Iraq war, Iran seeded the entrance to the Strait of Hormuz with Soviet contact mines.9 Alternatively, they could be used to inhibit amphibious forces attempting to come ashore. During the 1990-1991 Persian Gulf War, Iraq deployed sea mines to limit coalition forces’ ability to launch an amphibious assault.10 Similarly, during the Korean War, North Korean mining of Wonsan Harbor “prevented over 50,000 U.S. Marines from coming ashore and allowed the North Koreans to withdraw their forces.”11 However, swarming sea mines can play additional roles, such as protecting friendly vessels.
Advantages over Traditional Mines
Swarming sea mines have qualitatively better capabilities. Compared to traditional mines, swarming sea mines have drastically increased the threat through autonomous movement, broad area coverage, and information integration.
Autonomous Movement
Advances in robotics enable unmanned systems to maneuver and act without human decision-making.13 DoD’s Perdix drone swarm shares a “distributed brain” to make decisions and react to the environment.14 The swarm fully controls its own behavior without human direction, other than setting broad mission goals. Other autonomous systems such as the South Korean SGR-A1 gun turret can reportedly identify and engage targets.15 Although DoD policy does not allow autonomous weapons systems to select humans as targets, traditional sea mines already autonomously engage targets.16
Maneuverability enhances the psychological effects of minefields. Fear over encountering a minefield can affect behavior without inflicting damage. Once a vessel passes through a traditional minefield, it is often safe. However, a swarming minefield may move to a new area, adding new uncertainties.
Greater maneuverability enables drone-based naval mines to incorporate automated retreat rules. For example, after a specified time, drones may disarm and leave the area. Friendly vessels may then retrieve and redeploy them in another location. For traditional naval mines, retrieval is a highly fraught task because a retrieving vessel may inadvertently detonate the mine. Emplaced mines cannot be reused; swarming sea mines can.
Autonomous decision-making would enable swarming sea mines to identify and respond to changes in environmental conditions that could mitigate their effects. With traditional bottom mines on the seafloor, strong tides and currents can shift the mines.17 Swarming mines could recognize this shift and adjust.
Autonomous movement is a significant departure from the capabilities of traditional naval mines. While some advanced mobile mines such as the MK 67 Submarine-Laid Mobile Mine can be placed from afar, the MK 67 remains in place.18 Other naval mines are able to move with the current. None of these mines can position themselves intelligently.
Information Integration
The inter-connectivity of a drone swarm enables naval mines to integrate information from many different sensors. Sensor drones could incorporate traditional influence sensors, including magnetic, acoustic, and seismic sensors.19 Data from multiple sensors may be shared to minimize false positives. Sensor drones may roam freely, studying an area for potential targets, creating greater situational awareness. Alternatively, buried sensor drones could enable live battle-damage assessment. If an adversary vessel survives an initial strike, additional attackers may be called to follow and engage.
Swarming naval mines may be connected into broader intelligence and surveillance networks. Information from these networks could enable the swarm minefield to reposition based on adversary behavior. For example, naval intelligence may identify an adversary vessel about to enter a given area and relay that information to the drone swarm to maneuver into the vessel’s path.
While traditional naval mines are already capable of incorporating multiple sensors to prevent false positives, they are unable to share information with one another.20
Broad Area Coverage
Maneuverability and information integration would enable swarming sea mines to greatly increase the threatened area. Sensor drones can disperse broadly to provide maximum situational awareness. Information may then be relayed to other drones to engage an incoming target.
Like attack drones, sensor drones may be free roaming or stationary, though there are trade-offs. Free-roaming sensor drones may actively search an area looking for targets. This enables much broader coverage; however, communication ranges may limit the distance they can travel. Stationary sensing drones may float near the surface or bury themselves in the seafloor. Sensor drones that bury themselves minimize the profile presented to adversaries, lowering detectability. However, stationary drones lose the benefits of mobility, providing less area coverage.
The increased area coverage is efficient because fewer munitions would be required to control a given area. Mines will take up less space on friendly vessels while having the same impact. This is especially important for submarine-launched mines, because submarines have very limited storage capacity. Currently, to equip submarines with mines requires removing torpedoes at the rate of one torpedo for every two mines.21
Challenges
Despite these significant advantages, however, operationalizing the concept entails some significant challenges. None of these challenges appears insurmountable, and work is already being done to address them, but they must be considered for concept viability and to realize the benefits of swarming.
Undersea Communication
The ability of the swarm to function as a unit depends on drone communication. Underwater, this is a major challenge. Traditional communication methods are often based on electromagnetic transmissions that are ineffective underwater.22 Underwater communications must rely on acoustic communication, which is slower, has small bandwidth, and has high error rates.23 The lack of electromagnetic communication also prevents drones from using GPS guidance for coordination and localization.
Initial research points to the inclusion of relays and surface-based control drones as a solution (see footnote 5 for a brief typology of drone archetypes). To address the lack of underwater GPS penetration, Jules Jaffe and his research team incorporated GPS-localized surface buoys that emit acoustic signals.24 Their underwater drones passively receive the buoy’s signals and, based on the known location of the surface floats, determine their own location.25 Similarly, Thomas Schmickl and his research team use a “surface base station” emitting an acoustic signal for localization and establishing boundaries to ensure no drone gets lost in the ocean’s expanse.26 The station also receives status updates from the swarm, such as task completion.
From a military perspective, a surface control drone may be undesirable because it could be identified and targeted, neutralizing the minefield. To prevent this, control drones could be underwater with a GPS periscope extending above the surface to receive and transmit signals. Alternatively, swarms could incorporate redundant control drones. If one is eliminated, the minefield stays live.
More broadly, the underwater environment creates difficulties in countering adversary attempts to disrupt communications. An adversary is likely to target inter-swarm communication because if communications are disrupted, so too is the swarm.27 Unfortunately, the properties of underwater communication mean terrestrial jamming detection technologies do not operate effectively.28
Tethering and Reseeding
Reseeding a minefield is often a significant challenge. If most mines have detonated, the minefield offers little utility. Adding mines in hostile terrain while incur risk such as on January 18, 1991 when Iraqi forces shot down a mine-dropping A-6 aircraft.29 The mobility of drone swarms diminishes some of this challenge because the drones may be deployed from afar to move into position.
Reseeded mines must also tether to the swarm’s network. An added attack drone needs to integrate with the other attackers and with the broader sensor network. Reseeded drones need to recognize that they are a part of the minefield’s network and vice versa. It also requires the distributed brain of the swarm to incorporate the new drones into task assignment and overall control.30
Coordinated re-positioning removes some difficulty. If few attack drones have been destroyed, the other drones can fill any gaps. However, as the losses grow larger, or if the swarm had few attackers to begin with, adding attackers becomes a greater challenge.
Power
The availability of power limits swarm operations. On-board power is required to maintain communications, use propulsion systems, and operate and interpret the results of sensing systems. These requirements limit the amount of time the swarm can pose a threat.
One possible solution is sea-based charging facilities. Support ships could be created whose primary role is to recharge undersea drones, including swarming sea mines. They could also be used for swarm maintenance, reseeding the swarm, or long-range transportation. Alternatively, the Navy’s work on unmanned undersea pods could allow for undersea recharging.31 This would likely be most useful for mining friendly territory because the pods would need to be pre-positioned and adversaries could target them. As swarm size increases, so too will this challenge. Large swarms may also encounter queuing problems if only a few drones can charge simultaneously. Regardless of the solution, time spent traveling to and from recharging facilities also limits time in a mission area.
Conclusion
A 2001 National Research Council study painted a bleak picture of U.S. naval mine warfare: “The current U.S. naval mining capability is in woefully bad shape with small inventories, old and discontinued mines, insufficient funding for maintenance of existing mines, few funded plans for future mine development (and none for acquisition), declining delivery assets, and a limited minefield planning capability in deployed battle groups.”32 This holds true today: the Navy’s FY17 to FY21 budget anticipates spending only $29.4 million on acquiring offensive mines.33 Similarly, the FY17 to FY21 budget for the Navy’s only research and development program for mine systems is $56.9 million.34 All new mine development is relegated to converting Submarine-Laid Mobile Mine warheads for underwater drone delivery.
If networked swarms of sea mines represent the Navy’s future capital ship, that picture must be repainted. Drastically.
Zachary Kallenborn is a Senior Associate Analyst at ANSER pursuing broad research into the military implications of drone swarms.
The author would also like to thank Jerry Driscoll, Steve Dunham, and Keith Sauls for providing useful comments and edits on a draft of the article. Needless to say, any issues or mistakes are the author’s own.
The views herein are presented in a personal capacity and do not necessarily reflect the institutional position of ANSER or its clients.
References
1. Robert C. Rubel, “The Future of Aircraft Carriers,” US Naval War College Review 64, Autumn 2011, https://www.usnwc.edu/getattachment/87bcd2ff-c7b6-4715-b2ed-05df6e416b3b/The-Future-of-Aircraft-Carriers.
2. Bill Glenney, “Institute for Future Warfare Studies Wants Your Writing on the Capital Ship of the Future,” Center for International Maritime Security (CIMSEC), https://cimsec.org/institute-for-future-warfare-studies-wants-your-writing-on-the-capital-ship-of-the-future/33307
3. John Fleming notes the importance of visibility in conventional deterrence in John Fleming, “Capital Ships: a Historical Perspective,” Naval War College, July 12, 1993, 17, http://www.dtic.mil/dtic/tr/fulltext/u2/a266915.pdf
4. John J. Rios, “Naval Mines in the 21st Century: Can NATO Navies Meet the Challenge?” thesis, Naval Postgraduate School, June 2005, 1, www.dtic.mil/dtic/tr/fulltext/u2/a435603.pdf; “Mine Warfare,” Department of the Navy, Office of the Chief of Naval Operations and Headquarters U.S. Marine Corps, NWP 3-15 and MCWP 3-3.1.2, https://archive.org/stream/milmanual-mcwp-3-3.1.2-mine-warfare/mcwp_3-3.1.2_mine_warfare_djvu.txt.
5. Scott C. Truver, “Taking Mines Seriously: Mine Warfare in China’s Near Seas,” Naval War College Review 65, Spring 2012, https://www.usnwc.edu/getattachment/19669a3b-6795-406c-8924-106d7a5adb93/Taking-Mines-Seriously–Mine-Warfare-in-China-s-Ne; Bradley Peniston, “The Day Frigate Samuel B. Roberts Was Mined,” USNI [U.S. Naval Institute] News, May 22, 2015, https://news.usni.org/2015/05/22/the-day-frigate-samuel-b-roberts-was-mined.
6. Scott C. Truver, 2012.
7. In general, there are four drone archetypes: Attacker, Sensor, Controller, and Decoy (the ASCDs). Attack drones carry munitions or are themselves munitions. Sensor drones provide information about the surrounding environment. Control drones manage the swarm’s behavior to ensure the swarm can operate together, providing direct leadership or ensuring the operation of communication channels. Decoy drones serve no role other than to increase the apparent size of the swarm, creating psychological effects, or drawing fire for functional drones. This framework is the author’s own; however, it is consistent with others such as Jeffrey Kline’s Shooter, Scout, and Commander. Jeffrey E. Kline, “Impacts of the Robotics Age on Naval Force Design, Effectiveness, and Acquisition,” Naval War College Review 70, Summer 2017, https://www.usnwc.edu/getattachment/db52797a-a972-44cd-951b-f2b847b193b3/Impacts-of-the-Robotics-Age-on-Naval-Force-Design,.aspx.
8. “Department of Defense Announces Successful Micro-Drone Demonstration,” DoD news release, January 9, 2017, https://www.defense.gov/News/News-Releases/News-Release-View/Article/1044811/department-of-defense-announces-successful-micro-drone-demonstration/.
9. Gary Mortimer, “Chinese One Thousand Drone Swarm Smashes Intel Record,” sUAS News: The Business of Drones, February 13, 2017, https://www.suasnews.com/2017/02/chinese-one-thousand-drone-swarm-smashes-intel-record/.
10. Captain Gregory J. Cornish, U.S. Navy, “U.S. Naval Mine Warfare Strategy: Analysis of the Way Ahead,” U.S. Army War College, April 2003.
11. Gregory J. Cornish, 2003.
12. John J. Rios, citing Gregory K. Hartmann and Scott C. Truver. Weapons That Wait: Mine Warfare in the U.S. Navy. Updated Edition. (Annapolis, MD: Naval Institute Press, 1991), 231.
13. Determining appropriate rules of engagement is also a critical, related challenge; however, that is not within the scope of this article.
14. “Perdix Fact Sheet,” DoD Strategic Capabilities Office, June 1, 2017, https://www.defense.gov/Portals/1/Documents/pubs/Perdix%20Fact%20Sheet.pdf.
15. Alexander Velez-Green, “The Foreign Policy Essay: The South Korean Sentry—A ‘Killer Robot’ to Prevent War,” Lawfare, March 1, 2015, https://www.lawfareblog.com/foreign-policy-essay-south-korean-sentry%E2%80%94-killer-robot-prevent-war.
16. DoD Directive 3000.09: “Autonomy in Weapon Systems,” November 21, 2012, https://cryptome.org/dodi/dodd-3000-09.pdf.
17. Scott C. Truver, 2012.
18. National Research Council, Committee for Mine Warfare Assessment, “Naval Mine Warfare: Operational and Technical Challenges for Naval Warfare,” Washington D.C.: National Academy Press, 2001, 58.
19. For additional details on mine actuation mechanisms, see “Mine Warfare,” section 2.2.3.2, “Influence Actuation Logic.”
20. “Mine Warfare.”
21. “Mine Warfare.”
22. John Heidemann, Milica Stojanovic, and Michele Zorzi, “Underwater Sensor Networks: Applications, Advances, and Challenges,” Philosophical Transactions of the Royal Society A: Mathematical, Physical and Engineering Sciences 370, January 2012, http://rsta.royalsocietypublishing.org/content/370/1958/158.
23. Luiz Filipe M. Vieira, “Underwater Sensor Networks,” in Jonathan Loo, Jaime Lloret Mauri, and Jesus Hamilton Ortiz, Eds., Mobile Ad Hoc Networks: Current Status and Future Trends (Boca Raton, FL: CRC Press, 2012).
24. Jules S. Jaffe, et al., “A Swarm of Autonomous Miniature Underwater Robot Drifters for Exploring Submesoscale Ocean Dynamics,” Nature Communications 8, 2017, https://www.nature.com/articles/ncomms14189; for a more accessible version of their research, see Jesse Emspak, “Scientists Used Underwater Drone Swarms to Solve the Mystery of Plankton Mating,” Quartz, January 24, 2017, https://qz.com/893590/scientists-used-underwater-drone-swarms-to-solve-the-mystery-of-plankton-mating/.
25. Jules Jaffe, et al., 2017.
26. Thomas Schmickl, et al., “CoCoRo—The Self-Aware Underwater Swarm,” 2011 Fifth IEEE [Institute of Electrical and Electronics Engineers] International Conference on Self-Adaptive and Self-Organizing Systems, 2011, http://zool33.uni-graz.at/artlife/sites/default/files/cocoro_SASO_paper_revision_as_finally_submitted.pdf.
27. Paul Scharre, “Counter-Swarm: A Guide to Defeating Robotic Swarms,” War on the Rocks, March 31, 2015, https://warontherocks.com/2015/03/counter-swarm-a-guide-to-defeating-robotic-swarms/.
28. S. Misra, et al, “Jamming in Underwater Sensor Networks: Detection and Mitigation,” IEE [Institution of Engineering and Technology] Communications 6, November 6, 2012, http://ieeexplore.ieee.org/document/6353315/.
29. National Research Council, Committee for Mine Warfare Assessment, 2001, 18.
30. Some initial work has been done on scalable drone swarm control algorithms. See Payam Zahadat and Thomas Schmickl, “Division of Labor in a Swarm of Autonomous Underwater Robots by Improved Partitioning Social Inhibition,” Adaptive Behavior 24, 2016, http://journals.sagepub.com/doi/full/10.1177/1059712316633028.
31. Michael Hoffman, “Undersea Pods to Hold US War Supplies,” Defense Tech, January 16, 2013, https://www.defensetech.org/2013/01/16/undersea-pods-to-hold-us-war-supplies/.
32. National Research Council, Committee for Mine Warfare Assessment, 2001, 57.
33. “Department of Defense Fiscal Year (FY) 2017 President’s Budget Submission: Navy, Justification Book Volume 1 of 1, Weapons Procurement, Navy,” Secretary of the Navy, February 2016, 307, http://www.secnav.navy.mil/fmc/fmb/Documents/17pres/WPN_Book.pdf
34. “Department of Defense Fiscal Year (FY) 2017 President’s Budget Submission: Navy, Justification Book Volume 3 of 5, Research, Development, Test, and Evaluation, Navy, Budget Activity 5,” Secretary of the Navy, February 2016, 947, http://www.secnav.navy.mil/fmc/fmb/Documents/17pres/RDTEN_BA5_Book.pdf.
Featured Image: EMC Contact Mines aboard a Leberecht Maas class destroyer in Autumn 1940 (via Navweaps.com)