By Richard Mosier
Defining a warfare area’s mission and function is the foundation for all activities required to conduct mission area analysis to determine requirements, develop doctrine and tactics, and structure, train, and equip the fleet to accomplish the mission.
Within the U.S. Navy, the terms Information Warfare (IW), Information Operations (IO), and Information Operations Warfare are widely used but not well defined. Nor are they linked to provide coherent definitions from joint and service perspectives that are essential to successful communication regarding IW’s relationship to other warfare areas and supporting activities. The result is confusion and a lack of progress in structuring, training, and equipping the U.S. Navy to perform this emerging predominant warfare area.
The following are examples of how these terms mean different things to different groups:
Reference: Station Hypo, 14 Jul 16, “CWOBC, a Community’s Course“: “The Cryptologic Warfare Officer Basic Course (CWOBC) formerly known as the Information Warfare Basic Course (IWBC) is an entry level course for all officers, regardless of commission source, who are coming into the Cryptologic Warfare Officer (CWO) community. Six weeks in length with an average annual throughput of 154, the course focuses on Signal Intelligence (SIGINT), Electronic Warfare (EW), Cyber Operations, as well as security fundamentals and community history.” Inasmuch as the content of the basic course remained the same, the terms “Information Warfare” and “Cryptologic Warfare” appear to mean the same thing for this group.

Reference the BUPERS Information Warfare Community Management web page. It only addresses Information Professionals (1820), Cryptologic Warfare Specialists (1810), Cyber Warfare Engineers (1840), Intelligence Officers (1830), and Oceanography Specialists (1800), implying that together this aggregation of legacy support specialties constitutes Information Warfare. All of these are restricted line designators that by definition exercise command only over organizations that perform these specialties. There are no unrestricted line designators for specializing in and exercising Information Operations Warfare Commander (IWC) functions described in Naval Warfare Publication NWP 3-56 below.
Reference: NAVADMIN 023/16, DTG 021815 Feb 16, Subject: Information Dominance Corps Re-designated Information Warfare Community. The message states Information Warfare’s mission is: “providing sufficient overmatch in command and control, understanding the battlespace and adversaries, and projecting power through and across all domains.” This description of the Information Warfare mission is substantially different from the definition of Information Operations defined by Secretary of Defense, adopted by the JCS, and reflected in Naval Warfare Publications.
The Secretary of Defense defines Information Operations in DOD Directive 3600.1, dated May 2, 2013, as: “The integrated employment, during military operations, of information-related capabilities in concert with other lines of operation to influence, disrupt, corrupt, or usurp the decision making of adversaries and potential adversaries while protecting our own.” This definition was incorporated in Joint Pub 1-02 and Naval Warfare Publications.
Naval Warfare Publication (NWP) 3-13 Information Operations, Feb 2014, defines Information Operations as: “the integrated employment, during military operations, of information-related capabilities in concert with other lines of operation to influence, disrupt, corrupt, or usurp the decision making of adversaries and potential adversaries while protecting our own.” Paragraph 1-3 states: “Evolving joint and Navy doctrine has refined IO as a discrete warfare area, not just a supporting function or enabling capability, and the IE [information environment] as a valuable and contested part of the battlespace.”

Naval Warfare Publication (NWP) 3-56, subject: Composite Warfare Commander, Feb 2010, Paragraph 3.7 identifies twenty-three typical functions assigned to the “Information Operations Warfare Commander (IWC)” that are summarized below:
- Planning IO, EW, Military Deception, Operations Security, PSYOP, and Spectrum Usage.
- Developing, coordinating, and practicing preplanned responses for counter-surveillance, counter-influence, and counter-targeting in response to changes in the tactical situation.
- Recommending the EMCON profile and coordinating with ASWC to manage acoustic emissions in response to changes in the tactical situation.
- Controlling ES and EA assets, and coordinating employment of ES and cryptologic sensors.
- Conducting computer Network Defense (CND) and COMSEC monitoring.
- Paragraph 4.3.4 states; “The IWC establishes and maintains the tactical picture….” It also states: “[T]he IWC ….. achieves and maintains information superiority….and supports other warfare commanders.”
The term Information Operations is officially defined and documented. The term Information Warfare, though used extensively within the Navy, is not clearly defined, nor is it linked to Information Operations, resulting in confusion and limited progress.

For example, within the OPNAV Staff the N-2/N-6 carries the title Deputy Chief of Naval Operations for Information Warfare. He/she leads the “Navy Information Warfare Community” which so far is composed only of the legacy support specialties of Intelligence, Cryptology, METOC and IT. To date, there is little to suggest that the OPNAV N-2/N-6 has assumed responsibility for mission analysis, requirements definitions, and structuring, training, and equipping the fleet to achieve superiority over an adversary through Information Operations. Moreover, there is little suggesting recognition that Information Operations Warfare Commander (IWC) functions require performance in a command capacity (IWC), specialized training, and substantial systems functionality that has to be integrated with, rather than separate from, the combat systems that support other warfare areas.
CNO NAVADMIN 083/12, DTG 121702ZMAR12, Subject: OPNAV Realignment, lays out that the DCNO for Warfare Systems (N9) “is responsible for the integration of manpower, training, sustainment, modernization, and procurement readiness of the Navy’s warfare systems.” The N9 supplies leadership, guidance, and direction to the directors of Expeditionary Warfare (N95), Surface Warfare (N96), Undersea Warfare (N97), and Air Warfare (N98). The organization also oversees requirements and resource allocation across these warfare areas. Information Operations is not mentioned. From all indications, the N9 is not responsible for integrating IW/IO combat system functionality with the combat systems that support planning and execution in the traditional warfare areas. Given the functions of the IWC summarized above, combat systems integration is essential for mission success. This suggests the need for a well defined relationship between the N-9 and the N-2/N-6.
In order to eliminate confusion and realize the potential contribution of Information Operations to naval warfare, the U.S. Navy needs to formally (1) define the IW mission, (2) specify IW functions to be accomplished by personnel, organizations, and systems, and (3) assign IW organizational responsibilities. The following are proposed definitions.
Mission
Per JP 1-02, Information Operations is “the integrated employment, during military operations, of information-related capabilities in concert with other lines of operation to influence, disrupt, corrupt, or usurp the decision making of adversaries and potential adversaries while protecting our own.”
This definition, focused on “operations” or “employment” would be retained. However, it does not satisfy the JP 1-02 criteria of “mission”: “The task, together with the purpose, that clearly indicates the action to be taken and the reason therefore.” The mission statement should be focused not on employment, but on the warfare task, purpose, action to be taken and the reason therefore. This translates to the need for the term “Information Warfare.” The following is offered as a statement of the mission of Naval Information Warfare:
That portion of naval warfare in which operations are conducted to influence, disrupt, corrupt, or usurp the enemy’s human and automated decision making to gain warfighting advantages over the adversary, while protecting our own.
Functions
JP 1-02 defines “Function” as: “The broad, general, and enduring role for which an organization is designed, equipped, and trained.” The following is offered as a statement of the functions of Navy Information Warfare:
Naval Information Warfare functions are to achieve superior situation awareness and combat command decisions; influence enemy decisions; deny the enemy information superiority; disrupt enemy decision making; and protect and defend own force information and information systems from external or internal threats.
Tasks
JP1-02 defines “Task” as: “A clearly defined action or activity specifically assigned to an individual or organization that must be done as it is imposed by an appropriate authority. A discrete event or action that enables a mission or function to be accomplished.”
IW tasks are those tasks considered essential for the accomplishment of assigned or anticipated missions. After defining IW mission and functions, mission area analysis can proceed to identify mission essential tasks, and define required operational capabilities derived therefrom.
In summary, IW is a predominant warfare area that has the unrealized potential to be a major factor in prevailing in naval warfare with a near-peer adversary through the employment of Information Operations. A clear definition of IW missions, functions, and assignment of responsibilities for requirements, resource sponsorship, acquisition, and combat systems integration would serve to place this warfare area on a firm footing and serve a foundation for the realization of its significant potential contribution to combat success.
Richard Mosier is a former naval aviator, intelligence analyst at ONI, OSD/DIA SES 4, and systems engineer specializing in Information Warfare. The views express herein are solely those of the author.
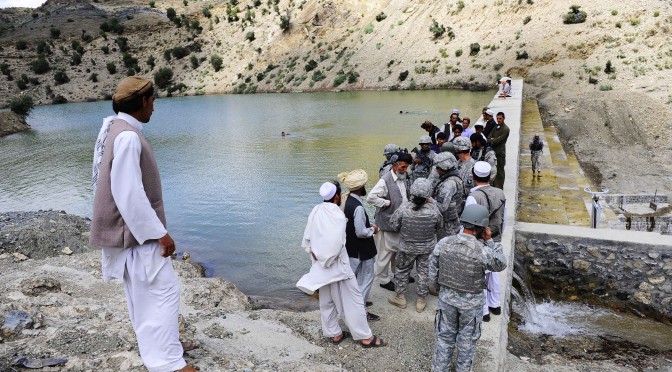
Featured Image: PENSACOLA, Fla. (Feb. 3, 2011) The Center for Information Dominance (CID) has become the first non-operational shore command approved for the newly created Enlisted Information Dominance Warfare Specialty pin. (U.S. Navy photo by Gary Nichols/Released)