Falling Out
Force development is much like agriculture. Seeds appear trifling things; but such small objects can engulf entire fields or grow to incredible height. Investing early in incubator programs can lead to huge changes in the future. When observed from a position of strength, the small changes garnered by others seem superficial rather than tectonic. The American defense establishment is missing those tectonic changes as China’s military begins the process of stealing a march in force development.

China is pursuing a broad portfolio of revolutionizing technologies. We have discussed in detail the potential opportunities for drone warfare on this blog and elsewhere. However, those working to reap such opportunities are not here in the U.S. where ideas are shared freely, but in the People’s Republic of China. Scientists in China have developed a system by which, with thought alone, an operator can control an aerial drone. Rudimentary technology at best, it is nonetheless a leap we have yet to take. Even at the beginning stages, it shows smoother control with a mental operator rather than a manual one. Although the US does seem dedicated to drone saturation, we have not moved past our initial uses and operation of them. Drones still require legions of remote operators rather than partial automation and direct connections with the men in the field. While we have yet to integrate our many exciting advances in automation and bionics, the PRC has grabbed a great leap forward and changed the very way they interact with drones.
China is also marching past us in more mundane military technologies. We have discussed the practicality and pragmatism of the Houbei versus our misbegotten LCS. Far from the risky investment in an in-shore knife-fighter some desired, LCS was held back as a conventional, do-everything (aka: nothing) combatant without the relative advantage in speed, strength, or resilience to give it any sort of field advantage. We essentially attempted to build a Ford RS300, but halfway through decided to finish it as an Isuzu Elf. Meanwhile, with the PLAN following a disciplined strategy for blue-water modernization, a stream of solidly-constructed and capable warships are pouring into the Pacific, making the failures of our current investment ever more evident. Our attempts at modernization in the air are just as white-washed; worse than the do-everything design of LCS, the new Joint Strike Fighter attempts to stuff the needs of every branch into one frame that doesn’t quite make anyone happy. Even basic capabilities, like anti-ship missiles, lag embarrassingly behind. While the U.S. still uses a sub-sonic cold-war relic, the PRC rolls out DF-21Ds. Where technology does branch out, it seems unnecessary, like the laser-guided Griffen Missile system on PCs that already have far-more capable Mod 2 25mm cannons. China’s more reasonable and planned forays into future technology have made our past-ideas decorated with sweet rims look ridiculous.
We are also shrinking from the one area in which we could claim total dominance: space. Although our nation is now in the mini-euphoria from Curiosity’s landing on Mars, most have forgotten that this is an achievement of a program started 8 years ago. Our current manned space program is dead. NASA shifted the lion’s share of investment to “earth sciences,” a realm already well-manned by all the scientists ON earth. China not only retains a manned space program, but advertises a plan for both the Moon and Mars. Even if such a schedule is a dream, at least they still have one. While this is not directly a military issue, it is a strong force multiplier. Space is the ultimate high ground. To lose dominance there undermines a vast number of U.S. capabilities.

Our mighty oak is rotting from within. Money is pouring into failed projects. Our Sailors are over-stretched and time is cut for the training/education necessary to add critical value to those personnel. Our priorities are skewed, millions of man-hours are lost to politically correct schools and rubbish ship-wide life-choices training. Meanwhile, the PLAN marches forward, steadily planting the seeds necessary to grow a modern blue-water navy supported by a far greater industrial base than anything the U.S. can muster. They are slowly reaching into the commons, as the face put forward by the U.S. becomes harder and harder to maintain. If we don’t get back into step soon, we may need that long-view of history to see just how far ahead of us the Chinese march has advanced.
Catching Up
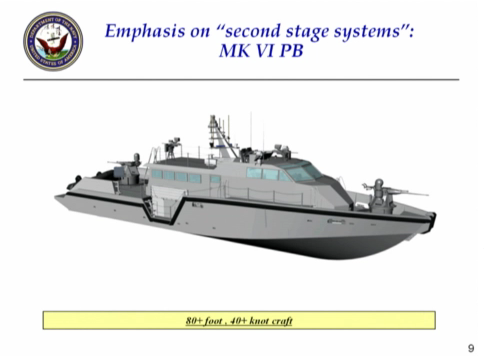
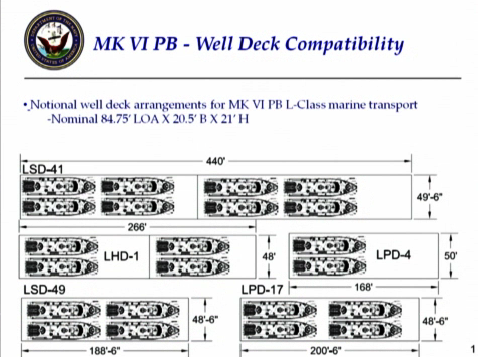
The effort necessary to regain our momentum would be disruptive, but not impossible. First, stubborn pride and sunk costs are no way to direct procurement. LCS must be cancelled. In its place, begin a vetting process for contracting a pre-existant hull to be built in the US, backed up by a low-mix of new coastal patrol crafts and the new MK VI’s. This would provide the desired coverage using fast, proven, and cheaper vessels that would save us billions in these tight times.
Where the LCS has many fine replacements, the JSF has crowded out the development of real alternatives. The diplomatic/trade capital invested also makes it an impossible program to cancel without painful follow-on consequences. However, the billions saved from LCS could fund a quicker turnover to automated and integrated ComBot technology, creating an “AEGIS in the sky” of super-fast autonomous aircraft and ComBots on the ground integrated with our fighting men and women. It’s a future closer than you may think. These new automated systems could lead to new systems to take on LCS’s failed missions, such as brown-water ASW and mine-sweeping.
With the US’s new technologies, we rely heavily on space. It is a commons commanding the ultimate high ground from which we guide our weapons, communications, and our intelligence infrastructure. Less concrete, but existentially more important, we must continue our investment in the development and exploration of space. The United States, at its very essence, doesn’t represent a set of borders, we survive as an idea. Being a nation undefined by a border, we must constantly strive beyond them. When the US landed on the Moon, we didn’t represent just ourselves, but all humanity. Such is a cause and driving force behind our constant success… a dream. To abandon that dream, even worse to cede it to the likes of the PRC, would be tantamount to ideological suicide. We must re-invest in our manned space program. This is not in defense of our physical commons, but in the commons of ideas, something to believe in. Much like the JSF and LCS programs, we don’t believe anymore. We’re going through the motions. We need to regroup and find a real direction towards the future, because the PRC marching past us.
Matt Hipple is a surface warfare officer in the U.S. Navy. The opinions and views expressed in this post are his alone and are presented in his personal capacity. They do not necessarily represent the views of U.S. Department of Defense or the U.S. Navy.