By Lin Yang Kang
The Internet has grown phenomenally since the 1990s and currently has about 3.5 billion users who make up 47 percent of the world population.1 Out of the 201 countries surveyed, 38 percent have a penetration rate of at least 80 percent of its population.2 The ubiquity and reliance on cyberspace to improve the efficiency and capability of government, military, and civilian sectors lead to the Internet of Things (IOT) for day-to-day operations and in this pervasiveness of the use of Internet lies the potential for devastating cyber-attacks.
This paper seeks to discuss the crippling effects and dangers of cyber-attacks and outline the defensive responses against and control of cyber warfare.
The lethality, and hence appeal of cyber warfare, lies in its asymmetric3 and stealthy nature. Little resource, such as teams of experienced hackers, is required to render a disproportional amount of devastating damage to the core and day-to-day operations of both the government as well as the military. Unlike conventional warfare where a military build-up and transportation of resources are tell-tale signs of preparation, cyber-attacks can be conducted without warning. In this regard, it is akin to covert operations, such as the use of Special Forces or submarines, with added advantage of not exposing soldiers to the risk of harm. Coupled with the inherent difficulty in pinpointing attribution,4 subjects of a cyber-attack are left with the choice of either doing nothing except to try to recover or to retaliate against the suspected attacker without concrete proof and lose moral high ground, neither of which is optimal.
An example of a well-coordinated attack demonstrating the covert nature of cyber warfare occurred in 2007 when the Estonian government and government-related web-services were disabled.5 Though no physical damage was inflicted, it created widespread disruption for Estonian citizens. While Russia was the suspected perpetrator, it was never proven or acknowledged. In 2010, it was discovered that Iranian nuclear centrifuges that are responsible for enriching uranium gas had been infected and crippled by a malware, codenamed “Stuxnet.”6 This successful insertion of this malware effectively set the Iranian nuclear program back for a few years and demonstrated an effective and non-attributable way7 to pressurize if not exert will without the use of military might as it achieved what the United Nations Security Council (UNSC) had hitherto failed to do, i.e., curtail the development of nuclear weapons by Iran.
The above examples illustrate the potential damage of small-scale and limited cyber-attacks. Extrapolating from these examples, it is conceivable that the damage from a successful large-scale cyber-attack on a well-connected country that relies heavily on IOT can range from disruption of essential services, crippling confusion and even operational paralysis of both government and the military. For the government, a cyber-attack across every essential means and aspects of daily living including but not limited to destruction of financial data, records and transactions, forms of travel, communication means, and national power grid create chaos and confusion resulting in psychological shock that will in turn sap the will and resilience of the citizens. For the military, the irony is that the more modern and advanced a military is with its concomitant reliance on technology and network centric warfare, the more vulnerable it is to a potential cyber Pearl Harbor attack that will render its technological superiority over its adversary impotent. Given the symbiotic relation between the government and the military, a successful simultaneous cyber-attack on both government and the military can achieve Sun Tze’s axiom that the supreme art of war is to subdue the enemy without fighting.
Given its unique nature and unmatched demonstrated potential for lethality, it is understandable the attractiveness of cyber warfare as an instrument of choice for all players, both state and non-state actors and even individuals. As with all other forms of warfare, the need for defense against should be proportional to the threat. It is a game of cat and mouse,8 where hackers seek to find security vulnerabilities while defenders attempt to patch them up as soon as they are exploited and redirect the attackers to digital traps, preventing them from obtaining crucial information or cause damages. Specialized cyber warfare military branches have been formed in many countries, and extensive cyber defensive measures and contingency plans are being developed by government, military, and civil sectors of states. Through inter-cooperation, potential attacks could be resolved in the shortest time possible and minimize disruption, while preventing future attacks. As the world begins to witness the increasing use of cyber warfare as a weapon, cyber-attacks may not be as easy to conduct as before as states that understand the lethality of such attacks seek to safeguard their nation.9
Beyond defense at the national level, there is a lack of well-defined norms on the rules of cyber warfare as the international law community is still interpreting how current law of war can apply to cyber warfare. Recently, Tallinn Manual 2.0 was published by NATO’s Cooperative Cyber Defence Centre of Excellence (CCDOE) and is to date the most detailed study of how existing international laws can govern cyber operations.10 However, it currently serves as a reference and is non-binding. It is crucial for nations to iron out the rules for cyber warfare together and abide by it, ensuring that it will not affect the lives of civilians and minimize potential damages to non-military installations by cyber-attacks and cyber warfare.
Cyber warfare is a real and growing threat which has the potential to create disruption that the world has yet to witness. As nations become even more reliant on cyberspace as it ventures into automation and smart cities, they need to invest adequately in cyber defense and ensure that this new frontier is well-guarded. Apart from dealing with it domestically, on an international level, rules of cyber warfare need to be clarified and be abided by the international community to safeguard civilians. Cyber warfare may be threatening, but if the international community abides by clarified rules of cyber warfare and has sufficient cyber defensive measures established, the potential devastation caused by cyber-attacks could be minimized.
Yang Kang is a naval officer from the Republic of Singapore and a freshman at the Nanyang Technological University (NTU) in Singapore currently studying Electrical and Electronics Engineering. Before attending NTU, Yang Kang underwent midshipman training in Midshipman Wing, Officer Cadet School of the Singapore Armed Forces and was appointed Midshipman Engineering Commanding Officer during the Advanced Naval Term, his final phase of training.
Bibliography
Barker, Colin. “Hackers and defenders continue cybersecurity game of cat and mouse.” ZDNet. February 04, 2016. Accessed March 28, 2017. http://www.zdnet.com/article/hackers-and-defenders-continue-cyber-security-game-of-cat-and-mouse/.
Davis, Joshua. “Hackers Take Down the Most Wired Country in Europe.” Wired. August 21, 2007. Accessed March 21, 2017. https://www.wired.com/2007/08/ff-estonia/.
Geers, Kenneth. Strategic cyber security. Tallinn: NATO Cooperative Cyber Defence Centre of Excellence, 2011.
Zetter, Kim. “An Unprecedented Look at Stuxnet, the World’s First Digital Weapon.” Wired. November 03, 2014. Accessed March 21, 2017. https://www.wired.com/2014/11/countdown-to-zero-day-stuxnet/.
“Cyber Warfare Integral Part of Modern Politics, New Analysis Reaffirms.” NATO Cooperative Cyber Defence Centre of Excellence. December 01, 2015. Accessed March 15, 2017. https://ccdcoe.org/cyber-warfare-integral-part-modern-politics-new-analysis-reaffirms.html.
“Global Cybersecurity Index & Cyberwellness Profiles Report.” April 2015. Accessed March 23, 2017. https://www.itu.int/dms_pub/itu-d/opb/str/D-STR-SECU-2015-PDF-E.pdf.
“NATO presents the Tallinn Manual 2.0 on International Law Applicable to cyberspace.” Security Affairs. February 05, 2017. Accessed March 25, 2017. http://securityaffairs.co/wordpress/56004/cyber-warfare-2/nato-tallinn-manual-2-0.html.
“Internet Users by Country (2016).” Internet Users by Country (2016) – Internet Live Stats. Accessed March 20, 2017. http://www.internetlivestats.com/internet-users-by-country/.
“Internet Users.” Number of Internet Users (2016) – Internet Live Stats. Accessed March 20, 2017. http://www.internetlivestats.com/internet-users/.
“The Asymmetric Nature of Cyber Warfare.” USNI News. February 05, 2013. Accessed March 20, 2017. https://news.usni.org/2012/10/14/asymmetric-nature-cyber-warfare.
“The Attribution Problem in Cyber Attacks.” InfoSec Resources. July 19, 2013. Accessed March 25, 2017. http://resources.infosecinstitute.com/attribution-problem-in-cyber-attacks/#gref.
1. “Internet Users.” Number of Internet Users (2016) – Internet Live Stats. Accessed March 20, 2017. http://www.internetlivestats.com/internet-users/.
2. “Internet Users by Country (2016).” Internet Users by Country (2016) – Internet Live Stats. Accessed March 20, 2017. http://www.internetlivestats.com/internet-users-by-country/.
3. “The Asymmetric Nature of Cyber Warfare.” USNI News. February 05, 2013. Accessed March 20, 2017. https://news.usni.org/2012/10/14/asymmetric-nature-cyber-warfare.
4. “The Attribution Problem in Cyber Attacks.” InfoSec Resources. July 19, 2013. Accessed March 25, 2017. http://resources.infosecinstitute.com/attribution-problem-in-cyber-attacks/#gref.
5. Davis, Joshua. “Hackers Take Down the Most Wired Country in Europe.” Wired. August 21, 2007. Accessed March 21, 2017. https://www.wired.com/2007/08/ff-estonia/.
6. Zetter, Kim. “An Unprecedented Look at Stuxnet, the World’s First Digital Weapon.” Wired. November 03, 2014. Accessed March 21, 2017. https://www.wired.com/2014/11/countdown-to-zero-day-stuxnet/.
7. The United States and Israel were allegedly responsible for this cyber attacked but as with the Estonian example, it was never proven or acknowledged.
8. Barker, Colin. “Hackers and defenders continue cybersecurity game of cat and mouse.” ZDNet. February 04, 2016. Accessed March 28, 2017. http://www.zdnet.com/article/hackers-and-defenders-continue-cyber-security-game-of-cat-and-mouse/.
9. “Global Cybersecurity Index & Cyberwellness Profiles Report.” April 2015. Accessed March 23, 2017. https://www.itu.int/dms_pub/itu-d/opb/str/D-STR-SECU-2015-PDF-E.pdf.
10. “NATO presents the Tallinn Manual 2.0 on International Law Applicable to cyberspace.” Security Affairs. February 05, 2017. Accessed March 25, 2017. http://securityaffairs.co/wordpress/56004/cyber-warfare-2/nato-tallinn-manual-2-0.html.
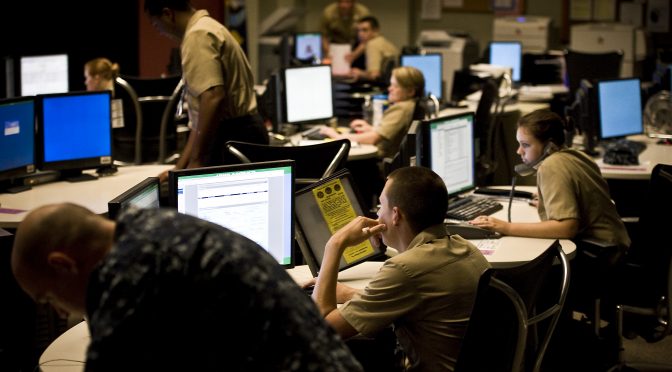
Featured Image: U.S. sailors assigned to Navy Cyber Defense Operations Command man their stations at Joint Expeditionary Base Little Creek-Fort Story, Va., Aug. 4, 2010. NCDOC sailors monitor, analyze, detect and respond to unauthorized activity within U.S. Navy information systems and computer networks. (U.S. Navy photo by Petty Officer 2nd Class Joshua J. Wahl)