It’s been quite a week for cyber issues in the news. CIMSEC’s own Matt Hipple has a must-read article in this month’s Proceedings about “Cloud Combat,” the coming blur between man and machine, and the rise of autonomous weapons systems. As a child of the ’80s, his writing couldn’t help but conjure in my mind the image of Governor Schwarzenegger in all his red-eyed glory as the Terminator. After reading Matt’s article, I skipped across cyberspace to Wired’s Danger Room, where I read about GPS spoofing and drones, a topic Matt also covers in his piece. Though the Wired post says that researchers only made a drone assume a crash course, it seemed all of a sudden that making drones take lives when we don’t want them to is more than plausible with today’s technology.
Autonomous weapons systems? Machines tricked into behaving badly? This common plot seems to be everywhere in our imagination: from Prometheus and the “Alien” franchise to Call of Duty: Black Ops II. In the world of the arts, drones, cyber attacks, and the loosening of man’s control over technology have constituted common plot elements throughout my lifetime. Now, it seems like technology is actually catching up with our imagination. It’s no wonder, then, that the military has placed so much emphasis on cyber warfare – it is an opaque medium. And we fear that which we don’t understand.
Fretting over the risks of modern technology, a pit of anxiety formed in my stomach as a dim memory from 2003 surfaced. Acting on it, I re-watched the last few minutes of Terminator 3. As autonomously-launched nuclear weapons decimate the human race, the character John Connor says the following lines:
By the time SkyNet became self-aware, it had spread into millions of computer servers across the planet. Ordinary computers in office buildings, dormitories – everywhere. It was software – in cyberspace. There was no system core. And it could not be shut down.
The Cloud! Nothing seems more threatening than this ethereal place, where all of our data resides to be taken or manipulated. And still more threatening code could reside there, as in the film. Members of my generation, I think, frequently think about these issues and feel powerless because the technology is already here. Pandora’s box has already been opened, so to speak, and we don’t know the awesome and potentially destructive implications of the rise of this technology. But… even though the new frontiers of technology are indeed threatening, there are many reasons to pause before buying all the bottled water you can find and speeding off to your bunker in the country.
Those of us living on the mid-Atlantic seaboard are still recovering from the so-called “Super Derecho” that felled trees and caused blackouts that for some are only being repaired now. As the Washington Post noted earlier this week, an Amazon data center was a casualty of the storm and the popular Netflix, Instagram, and Pinterest applications were all affected. Despite the fact that the Internet’s predecessors were specifically designed to be survivable, The Cloud, data feeds for our drones, and all of the other cyber-boogeymen we love to fear reside in physical places as vulnerable to real-world events as you or I.
This truth brings me to the title of the post: for those of you wishing to dispel some of your fears of our cyber-frontiers, the book Tubes: A Journey to the Center of the Internet is a great place to begin. The title is a riff on Sen. Ted Steven’s famous declaration that “the Internet is a series of tubes,” which rose to become a prominent internet meme. The author, Andrew Blum, essentially confirms Sen. Steven’s much-lampooned statement. Even in our wireless age, there is still a huge physical infrastructure supporting the internet – much of it tubes: fiber optics, transoceanic cables, and the like. This physical infrastructure needs power and cooling and is as vulnerable to fires, power outages and – most importantly – the destructive agency of man.
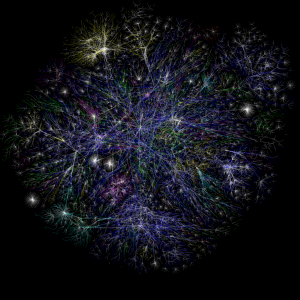
For a military reader, Tubes illustrates a useful lesson: as much as we talk about cyber warfare and the ability of malicious computer programs like the StuxNet virus to affect the physical world, the physical world’s affect on the cyber realm is equally as important. In fact, the structure of the Internet may be particularly vulnerable, according to scholars. A paper published by Doctors Cohen, Erez, ben-Avraham, and Havlin from 2000 says that the removal of a few key sites from some networks could bring them down entirely.
So, for the time-being, it makes sense to pierce the veil covering the Internet, machines, and what we’re doing with them and stop our hand-wringing over Judgement Day. Andrew Blum’s engaging writing and deft manner of illustrating complex issues simply are perfect for the layman who doesn’t know a TCP/IP protocol from a toaster. When it seems we’re a keystroke away from a technological armageddon, Tubes rises above the cacophony of fear-mongering and suspicion and reminds us that our technological creations are as vulnerable as we are — for now.
LT Kurt Albaugh, USN is President of the Center for International Maritime Security, a Surface Warfare Officer and Instructor in the U.S. Naval Academy’s English Department. The opinions and views expressed in this post are his alone and are presented in his personal capacity. They do not necessarily represent the views of U.S. Department of Defense or the U.S. Navy.
