By LCDR Robert “Jake” Bebber, USN, and Dr. John Hemmings
The most significant foreign policy debate in Washington at the moment is how to frame the emerging strategic competition with People’s Republic China (PRC), with foreign policy elites arguing whether we are in a “cold war” with China or something entirely different. The stakes of the debate are considerable because it will decide how the United States develops policies for competing with the PRC and how it frames that competition with allies and partners.
On the “against” side (those who disagree with framing the competition as a “cold war”), there are two basic approaches. The first is to argue that the United States should not engage in a cold war with the PRC – a prescriptive argument – based on the argument that the U.S. and PRC are too deeply intertwined to have a cold war and must cooperate across a range of international issues, including climate change, non-proliferation, North Korea, and COVID-19.
The second argument is that although the U.S. and PRC are engaged in a strategic competition, it should not be framed as a “cold war.” This is a “historical fallacy” argument based on differences between the current state of competition and that which existed between the U.S. and Soviet Union. Most recently, Richard Fontaine and Ely Ratner made this argument in the Washington Post, writing that the essential features that made the Cold War what it was – two coherent blocs arrayed against each other, with little or no economic integration – are missing.
While the positions laid out above have merit and although the current competition between Washington and Beijing has marked differences from the Cold War, we believe we can still learn from historic frameworks like the Cold War and that it provides a number of benefits for the U.S. in doing so.
Four Arguments in favor of a Cold War Framework
In this essay, we make four arguments for calling the U.S.-China competition a “cold war”:
- The Cold War template provides Western political elites with a compelling narrative on why Western publics must bear the burdens imposed by a competition that may occur over many decades. It also shapes a “common approach” towards our adversaries within society at large.
- There is a structural similarity between the Cold War and the current competition, as a potential hegemonic transition takes place between two nuclear powers, thus diffusing competition horizontally, below the threshold of war into other areas of competition.
- The United States and the PRC have different political and economic ideologies with different approaches toward state power. Under China’s president, Xi Jinping, these have become more pronounced rather than less, causing friction between the two powers. What’s more, Chinese leaders view themselves to be in a competition with the West. A Cold War analogy acknowledges Chinese claims about the ideological competition.
- The Cold War template provides Western policymakers with both a toolset and point of comparison for constructing policies that will allow the West to weather long-term competition across multiple sectors, socialize allies, counter all-pervasive political warfare, and develop the military-industrial strategies for long-term competition.
We argue that the debate over whether the Cold War framework should apply to the U.S.-China competition is missing key components, and that once applied, they support the utility of the framework.
Policy makers must engage the American population to once again take up the burden of leading its friends, allies, and partners in a global, ideological struggle for an indeterminate amount of time. Instead, policy elites remain fixated on whether to label this emerging competition as a “cold war” or not. But in that debate, neither side seems to consider that it is not the elites, but the taxpayers who will be crucial in supporting this competition. To that end, elites must meet taxpayers where they are.
Meeting Them Where They Are
As Michael J. Green discusses at the outset of By More than Providence (2017), there is even a debate whether democracies like the U.S. can ‘do’ grand strategy.1 This argument has been leveled against U.S. foreign and defense policy2 a number of times and has much to do with the pluralistic style of governance, required consensus-building, and weak power of the executive over the economy and other tools of statecraft. However, for democratic states to compete well, they need to frame their competitions well with their constituencies. The strategic competition with the PRC will require a reorganization – at the very least – of a great many of the tools of U.S. statecraft, in the bureaucracy, in society, in education, and in the media.
While the previous Administration restricted U.S. technology companies and businesses in their dealings with the PRC, the need for a compelling and overarching national narrative is increasing. Much of the national debate around supply chain security, leading to “decoupling” or “partial disengagement” from the PRC has suffered because it is not clear to what extent the state requires those who seek the nation’s fortune to make way to those who seek its security. Critics of decoupling or of restrictions on PRC tech companies continue to make counter-arguments based on costs, revealing a stark lack of understanding of the extent of the forthcoming competition. If the United States is going to expect its finance, tech, and innovation sectors to restrict their dealings with the PRC, they must do more than simply pass regulatory measures and legislation.
There is also the issue of paying for the strategic competition and the growing alarm among many on both sides of the political spectrum over the structural fiscal challenges America faces. At the same time that these challenges must be addressed, policy makers must justify to taxpayers why in a time of recovery from the pandemic, several hundred billion dollars, or perhaps more, must be devoted toward defense, the intelligence community, public diplomacy, strategic communication, research and development, and other efforts critical to national security.
The U.S. policy community must explain to U.S. taxpayers why they are expected to pay a larger proportion of their taxes toward defense. U.S. defense spending between 1949 and 1990 (between five and ten percent of GDP) was at historically high levels for nearly five decades. Today, even though defense spending barely constitutes three percent of GDP, it would be absurd to expect the public to be willing to shoulder this type of burden for anything less than a war, “cold” though it might be. Finally, and perhaps more importantly, the U.S.-Soviet Cold War is replete with examples of bureaucratic, education-funding, and departmental organization that helped the United States compete.
Preparing the American people for a long-term competition and potential conflict will come against the backdrop of formidable social, economic, and domestic obstacles not easily overcome. They include income disparity and labor issues in an economy that has been offshoring its “middle” skill manufacturing jobs for decades. In addition, the United States is undergoing an opioid crisis that creates pressure on already-wide social disparities in health coverage and access to public resources. Finally, social and political divisions between the conservative and liberal wings of U.S. society, media, and political elites have begun to widen, creating tension points across a range of issues including immigration, policing and society, race-based politics, and religion. These are the daily realities of the general population. In a crisis, these social and domestic tensions will only be exacerbated.
These social, economic, and health conditions are the backdrop to a well-documented fiscal challenge that Congress faces. Recent policy decisions on taxation and emergency spending as a result of the global COVID-19 pandemic have added to the problem. This is not to say that they are insurmountable. The U.S. still has the world’s largest economy, and with more than $20 trillion in gross domestic product annually, the resources are available, even if the political will remains elusive. The fiscal burden of creating and sustaining American power is likely to grow. This burden will come at a time when it will be incumbent on decision makers to address the entire scope of national taxation and spending. Hard trade-offs will be required.
Yet fiscal constraints are only one piece of the puzzle. Even if the resources were readily available, it is not entirely clear that the population of 2020 is particularly interested in competing. The first Cold War was born out of the Second World War, and early system shocks caused a public reappraisal of U.S. efforts to rebuild the world order while being confronted with a global Communist movement that had other designs. That context is missing for today’s generations.
Part of this is due to the nature of how the Cold War ended and the brief, “unipolar moment” the United States and its Allies enjoyed. During the unipolar moment, little effort was given to recapitalizing the institutions necessary to meet a new, peer challenger. Even anti-communist stalwarts argued that it was time for America to become a “normal nation,” and shed the burden of global leadership. The lack of an existential threat made such calls more appealing.
Recent polling suggests that a smaller portion of younger generations consider America an “exceptional” nation. Significant gaps exist between generations on perceived threats to America, with Millennials pointing to “climate change” (62%) as a bigger threat than “the development of China as a world power” (35%), “North Korea’s nuclear program,” (55%) or the “rise of authoritarianism around the world” (42%). Now as one ages and experiences the world, the perception of threats changes. Generations are not monolithic and views do not remain etched in stone. Evidence suggests that the public is growing far more wary of China as a threat, and the recent global COVID-19 pandemic and the Chinese leadership’s complicity in covering up the danger may further incur the American public’s anger. Fortunately, the vast majority of Americans still believe that a future with U.S. leadership is far better than a world led by Beijing.
An Ideological and Existential Fight
Like the original Cold War, the ongoing competition between China and the United States is openly ideological in nature, and there will be a winner and a loser. Nadège Rolland notes that the implications of this struggle for “discourse power” and the significant resources that Beijing is pouring into expanding its media footprint and activities overseas, indicating “a yearning for a partial hegemony, loosely exercised over positions of the ‘Global South’ – a space that would be free from Western influence and purged of liberal ideals.”3 While it has been a long-cited trope that the PRC is “communist in name only,” there are abundant signs that Xi Jinping has sought to reassert the primacy of Marxist-Leninism, reinvigorate the centrality of the Chinese Communist Party, and hold up Socialism with Chinese characteristics and China’s unique development model as exports to the world.4 In addition to a string of campaign slogans, speeches, and policies meant to reinforce the importance of the Party’s Marxist heritage, it is clear from Xi’s internal speeches that he holds deep ideological convictions and began promoting them from the earliest days of his leadership.
In one early speech, given to CCP cadres in 2012, he argued that Chinese socialism was not only in competition with western liberalism and capitalism, but was destined for eventual dominance: “We firmly believe that as socialism with Chinese characteristics develops further, our system will inevitably mature; it is likewise inevitable that the superiority of our system will be increasingly apparent; inevitably, our country’s road of development will have increasingly greater influence on the world.” He continued, “But the road is tortuous. The eventual demise of capitalism and the ultimate victory of socialism will require a long historical process to reach completion.”
That Xi and other senior leaders see themselves in an ideological struggle vis-à-vis the West is also evident in the infamous Party memorandum, known in the West as “Document 9,” circulated by the General Office in April 2013 around the time that a general crackdown of human rights lawyers, academics, and media outlets was taking place. The memorandum asserted that “the current situation [is] a complicated intense struggle”, naming seven “perils,” including Western constitutionalism, civil society, “nihilistic” views of history, universal values, and the promotion of “the West’s view of media.”
In recent years, PRC leadership has begun to talk about exporting China’s “unique development model,” with Xi stating in 2017, “[China] offers a new option for other countries and nations who want to speed up their development while preserving their independence.” As Elizabeth Economy and others have written, this takes place primarily in the supply of training of foreign officials on its development model and distinctly authoritarian techniques, such as guiding public opinion, at new leadership academies, such as the Baise Cadre Academy, based in Guangxi. Most recently, Beijing responded to the COVID-19 crisis by framing it as a battle of systems, between its own handling of the crisis, and the handling by democratic states.
The Tools and Rules Still Apply
Historically, great powers competed for regional or global hegemony through conventional wars,5 such as the Napoleonic Wars, or the First and Second World Wars.6 In all three instances, rising powers sought to challenge the status quo power or order, and establish their own hegemonic orders, suited to their individual national preferences. The United States and USSR were not fated to have a cold war, but driven to it by the impossibility of using war as a matter of statecraft in resolving their hegemonic competition. The mutual possession of nuclear weapons caused a stalemate and as a result, the confrontation became ‘colder’, waged through what Rogers calls “a plethora of proxy conflicts and with an array of instruments, deliberately designed to get underneath the escalatory ladder.” Hegemonic competitions between nuclear powers or nuclear blocs cannot be resolved in the historic manner. As a result, competition is diffused horizontally in sectors like technology, political warfare, sports, intelligence, media & discourse, and of course in indirect proxy wars, such as the Vietnam War and the Soviet War in Afghanistan.
The current competition between the United States and the PRC occurs across multiple sectors. It takes place in the military sphere, albeit at the gray zone level, or in planning and tactics – such anti-access/area denial. Competition also occurs at the level of international governance as the PRC begins to amass more influence among United Nations agencies (it leads four agencies, more than any other nation), leading to criticism from the United States that Beijing uses such agencies for its own national or geostrategic objectives.
Conflict also occurs in the media sector as Xi Jinping consolidated editorial control over most of China’s media outlets through changes made between 2013 and 2019.7 A massive outward push to those same media outlets to “tell China stories well” (jianghao zhongguo gushi) overseas, in conjunction with Beijing’s greater strategic goals has resulted in a growing bifurcation between Chinese and Western media.8 In response to the PRC’s drive to create positive external propaganda (waixuam), the U.S. ordered Chinese state propaganda organs inside the United States to register as foreign agents. In response, three major U.S. news outlets were banned from China.9
There is also a growing competition in the sectors that constitute civil society, cultural exchange, and education. The most recent evidence of this has been the American decision to restrict Chinese graduate students who have proven links to military institutions in the wake of a revival of China’s Thousand Talents program. It has also impacted the media, as policies under Xi Jinping began to promote a “discourse power” in a battle between Western media and Chinese state media.
The “character” of a cold war may have changed, but its “nature” has not.
As Mahnken has argued, many of the tools used by the United States during the Cold War still apply today as they are enduring sources of national statecraft and power. Alliance management, defense policy, arms control and competition, economic relations, political warfare, and internal security remain central concerns. He notes that the range of instruments of power the U.S. used was broad, and that today’s debate over competition seems to lack the scope of the Cold War. He writes “there has been much less debate over the role that arms control, industrial policy, industrial mobilization and internal security may play” compared to the Cold War.
Blanchette further articulates that a central feature of the Cold War was the protection and promotion of our American values and living up to the standards upon which the Republic was founded. He notes that early architects of America’s Cold War strategy, George Kennan and Paul Nitze, pointed to building “a successfully functioning political and economic system,” one that gives America the “courage and self-confidence to cling to our own methods and conceptions of human society.”
In this respect, the usefulness of the Cold War framing becomes more apparent. Half of the American population was alive for some or all of the Cold War, though that memory is growing distant. Yet there remains a residual notion among them of the gravity of the competition, its existential nature, and its costs.
Conclusion: The Cold War Frame Works, But You Have to Make the Case
In laying out our argument on why we believe the cold war framework is not only useful but necessary for the future of U.S. policy toward China, we have made certain key assumptions. The first of those is that the two powers will remain on a par for some decades to come. This is because Chinese advantages – excellent infrastructure, many more graduates in engineering, computing, and centralized planning – are balanced out by their disadvantages of an ageing and shrinking workforce, a growing tendency towards political control of the economy, and a costly internal security system. By that measure, U.S. social and political disarray at home is balanced out by the American advantages of a much-better educated and international workforce, access to two seas, and continental resources. For this reason, both states are likely to remain peer competitors for some time, with their ideological and geopolitical differences promoting a decades-long state of competition.
With these basic assumptions, it follows that it would be the most profound failure of policy for the United States to execute a grand strategy designed to compete with the People’s Republic China without popular consensus and support. Indeed, it would be disastrous. This is more important for younger generations as it is they who will largely face most of the sacrifice. The underlying assumption behind competing with China is that the American people are invested in the cause. If that assumption is misplaced, then the strategy will not be resourced adequately.
This will require not only public debate, but also public accountability, and the willingness to craft policy and strategy around the constraints of public opinion. While public opinion can be moved, the case must be made. This must be central to American strategy to compete and win this new cold war. The current complacency regarding the public’s declining trust in institutions and America’s role in the world is dangerous. Foreign powers are actively engaged in strategies to undermine political legitimacy and resiliency, but they need only accentuate the trends that were already present.
Jonathan Ward explains how the leaders of the People’s Republic of China have used economic engagement with the United States to bring it to the brink of the end of American power. Victory in their eyes is “the building of a superpower, and the restoration, as China’s leaders see it, of China’s position of supremacy among all nations.”10 Like the first Cold War, this one is also a conflict in which there will be a winner and a loser. It will be existential in nature, as the PRC challenges fundamental liberalism, respect for free markets, and democratic ideals within China and in the international system. The decade of the 2020s – much like the early years of the first Cold War – will shape the contours of this new Cold War. The window of opportunity is fast closing on America’s ability to organize its society to prepare to defend its interests and the cause of freedom. This is worth fighting for. But it cannot be defended without the support of the American people and the support of its allies abroad. It is a political case that must be made at all levels of government and society. It will require a renewed effort toward public education, and frank, honest debate about the sacrifice required. To best make the case, policy makers have to meet the American public where they are, using terms that convey the gravity of the situation and the stakes involved.
LCDR Bebber is a Cryptologic Warfare officer currently assigned to Information Warfare Training Command Corry Station, located in Pensacola Florida. He welcomes your comments at jbebber@gmail.com.
Professor John Hemmings is an associate professor at the Daniel K. Inouye Asia Pacific Center for Security Studies. He writes in his own personal capacity.
Endnotes
1. Green, Michael J., By More than Providence: Grand Strategy and American Power in the Asia Pacific since 1783, (New York, Columbia University Press, 2017), pp.2-5.
2. For examples, see: Betts, Richard K. “Is Strategy an Illusion?” International Security, 25, no.2 (Autumn 2000), p.40., Friedberg, Aaron, “Strengthening US Strategic Planning,” in Avoiding Trivia: The Role of Strategic Planning in American Foreign Policy, ed. Daniel W. Drezner (Washington DC, Brookings Institutional Press, 2010).
3. Rolland, “China’s Vision for a New World Order”, NBR Special Report 83, 27 January, 2020.
4. Economy, “Yes Virginia, China is exporting its model”, Council of Foreign Affairs Blog, 11 December, 2019.
5. For examples, see: Modelski, George, Long Cycles in World Politics, (Basingstoke, Hampshire, Macmillan Press, 1987); Wittkoph, Eugene R. World Politics: Trend and Transformation, 12th Edition (Belmont, Ca., Wadsworth Publishing, 2008).
6. For examples, see: Kennedy, Paul, The Rise and Fall of the Great Powers: Economic Change and Military Conflict from 1500 to 2000, (New York, Vintage Books, 1989); Mead, Walter Russell, God and Gold: Britain, America, and the Making of the Modern World.
7. Brady, Anne-Marie, “Plus la Change?: Media Control Under Xi Jinping”, Problems of Post-Communism, Vol. 64, Issue 3-4, 2017, pp.128-140.
8. Huang, Zhao Alexander, Wang Rui, “Building a Network to “Tell China Stories Well”: Chinese Diplomatic Strategies on Twitter”, International Journal of Communication, Vol. 13 (2019).
9. “China to restrict journalists from three major newspapers” BBC, 18 March, 2020.
10. Jonathan D. T. Ward, China’s Vision of Victory (Atlas Publishing and Media Company, 2019).
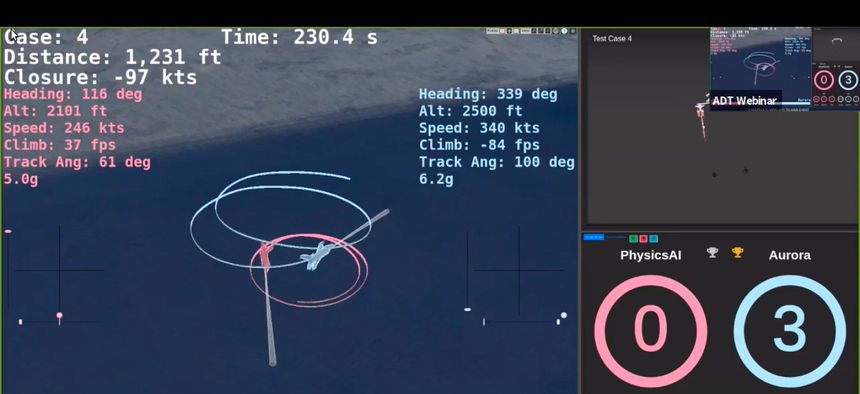
Featured Image: People’s Republic of China, People’s Liberation Army (Navy) frigate PLA(N) Yueyang (FF 575) steams in formation with 42 other ships and submarines representing 15 international partner nations during Rim of the Pacific (RIMPAC) Exercise 2014. (U.S. Navy photo by Mass Communication Specialist 1st Class Shannon Renfroe/Released)