By Shane Halton and Ryan Hilger
“From a proud tower in the town, Death looks gigantically down.” —Edgar Allan Poe
In late January 2023, the American public came into close, almost personal contact with a portion of China’s globe-spanning surveillance complex as a high-altitude balloon drifted across the United States. The balloon maneuvered and loitered over American intercontinental ballistic missile installations and other sensitive national security sites before the President ordered the balloon shot down off the coast of South Carolina. Imagery and the recovered debris cut against the Chinese narrative of a simple weather balloon – it was designed to gather intelligence and communicate it back. Congress and the American people demanded answers as to how a balloon could get into the United States almost untracked. A joint statement from Representatives Mike Gallagher (R-WI) and Raja Krishnamoorthi (D-IL) stated that “The Chinese Communist Party should not have on-demand access to American airspace” and that the threat from China “is here at home, and we must act to counter this threat.”1
The revelation that Chinese high-altitude surveillance balloons may have crossed the United States before unsettled national security leaders and the American public. Suddenly, a threat normally contained to the Western Pacific was made tangibly real to the average American. In Helena, Montana, a retired state judge told The New York Times: “I can’t believe they are spying on Billings, [Montana]… There’s not much there.”2 American security officials reported to the press that the Chinese balloon surveillance program had conducted operations in 40 countries across five continents.3 At least one theory rapidly emerged that the operation was a practice run for a high-altitude electromagnetic pulse attack or delivery of other effects.4 While Americans understood on some level that China had satellites and other systems capable of monitoring them, the drifting balloon became urgently personal and real, with several news outlets reporting this as a “Sputnik moment” for the country.5 In the 1950s, the Soviet Union’s Sputnik satellite’s constant beeping across the night sky profoundly and fundamentally altered how Americans perceived the Soviet Union and behaved in response.
We have been here before. The concept of a “hyperobject” can help provide national security leaders with a new framework to grasp, understand, and engage with China’s C4ISRT complex.
What is China’s C4ISRT Complex?
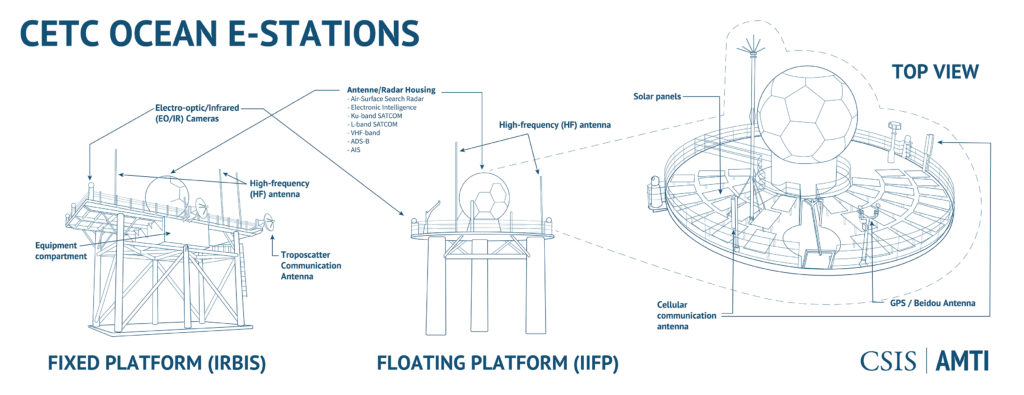
C4ISRT is a long-range network of active and passive sensors designed to identify, track, target and engage hostile forces across warfare domains (air, subsurface, surface, etc.). In addition to sensors and datalinks, the concept also encompasses the thousands of human analysts and IT professionals working to process and make sense of all the data. Each node —human, sensor, or otherwise—is linked via a complex web of network connections.
What separates a C4ISR network from a C4ISRT network is Targeting (the ‘T’)—the ability to use sensor data from a variety of systems to accurately direct long-range fires. If the data collected by the sensors lack sufficient detail or is “old” (as in out of date) it cannot be used for targeting precision weapon systems. As Beijing’s 2019 defense white paper, China’s National Defense in the New Era, states, the operational requirement for greater data fidelity, speed, and accuracy has compelled the Chinese military to continue investing heavily in both “informatization,” the development and deployment of ever more sensors to fill gaps and provide overlapping coverage, and “intelligencization,” the use of machine learning programs to assist in processing all the data collected.6 Both terms have grown in prominence through China’s last two defense white papers in 2011 and 2015. The combination of this evolving C4ISRT complex with modern precision weaponry creates non-linear battlespace effects greater than the simple sum of their constituent parts.7

Hyperobject as Conceptual Framework
Taken as a whole, China’s C4ISRT complex is best described as a “hyperobject,” a term first pioneered by philosopher Timothy Morton in his 2013 book Hyperobjects: Philosophy and Ecology After the End of the World. As defined by Morton, hyperobjects are very large objects distributed unevenly across time and space that operate at non-human timescales.8 Hyperobjects are not an abstraction or an intellectual parlor game. In fact, Morton’s goal is to refocus modern philosophy toward engaging with real objects in the real world and away from what he believes is a dead-end of recursive abstract analysis. Morton writes “Hyperobjects are real whether or not someone is thinking of them. Indeed, for reasons given in this study, hyperobjects end the possibility of transcendental leaps ‘outside’ physical reality.”9
In Hyperobjects, Morton draws the majority of his examples from ecology and the physical sciences, citing the sum total of all plutonium created since 1942 as a hyperobject par excellence.10 A primarily man-made chemical element that occurs very rarely in nature, plutonium is currently spread unevenly across the Earth’s biosphere, densely gathered in nuclear weapons caches, power plants, and storage facilities.
One key feature of hyperobjects is their ability to impact human social behaviors. Morton describes this feature as a hyperobject’s viscosity – its ability to enter our mental frameworks and get stuck there. In the case of plutonium, the combination of its radioactivity, its historic use in extremely destructive weapons, and its 21,400-year half-life means that even when plutonium is stored out of sight in nuclear weapons bunkers or at the plutonium waste store site at Savannah River, South Carolina, it is never out of mind. The existence of plutonium has compelled humans to alter laws, customs, and individual behaviors to account for the plutonium hyperobject they now share the planet with. During the Cold War, plutonium preoccupied national leaders in the United States and Soviet Union for decades and shaped how they engaged with each other.
In addition to their large, unevenly distributed mass, or their scale and viscosity, Morton notes two other distinctive features of hyperobjects – non-locality and the way in which they operate at non-human timescales. Non-locality means that a human being will only ever experience a part or portion of a hyperobject, never the whole hyperobject. We see one balloon over Montana but a dozen Chinese spy satellites whiz overhead each day, barely registering in Americans’ consciousness. Hyperobjects’ ability to operate at non-human timescales follows a similar logic. You might occupy the planet at the same time as a chunk of plutonium but, owing to its very slow rate of decay, it will outlast you, your family, and possibly your civilization. It is important to note that “non-human timescales” can refer to hyperobject behaviors that occur very quickly over a short period, such as a machine speed kill web, and not just slowly over a relatively long period as is the case in plutonium decay. The point is that a hyperobject’s timescale is out of sync with human biological, social, and organizational speeds.
Does China’s C4ISRT complex, taken as a whole, qualify as a hyperobject? An analysis of each of the four characteristics of hyperobjects indicates that it does.
Scale. China’s efforts to construct a C4ISRT complex began with the deployment of air surveillance radars along China’s coastline during the Cold War and greatly accelerated in the early 2000s with the deployment of modern active and passive surveillance systems along the Taiwan Strait. Over the last decade, China has supplemented its air and maritime surveillance capability with new, indigenously produced sensors designed to search the undersea domain as well as dozens of new spy satellites. Collectively, this sensor network is assessed by Western analysts to cover at least the Western Pacific, out to Guam, if not further.11

In addition to these investments in sensor capabilities, China’s military underwent significant organizational reforms in 2017-2018. The People’s Liberation Army is now organized into five Joint Theater Commands, each responsible for a different geographic area: Eastern Command is responsible for Taiwan; the Southern Command for the South China Sea; Northern Command for Russia and the Korean peninsula; Western Command for India and Tibet; and Central Command for Beijing and central China.12 This division of labor along geographic lines has simplified the human and organizational dimensions of the C4ISRT complex, making it more focused and efficient by aligning the sociotechnical aspects of the C4ISRT complex to optimize information flows, use of national resources and technical means, and joint planning for theater operations and achieving desired national outcomes.13
As Western observers have watched the Chinese C4ISRT network expand in scale, the influence of that growth, the near global reach of the system, and the continual expansion and alignment of resources and capabilities has altered the way in which Western policymakers perceive the system and the threat it poses. Two decades ago, the Chinese C4ISRT complex was an afterthought, easily accounted for and countered with existing tactical means. Today, however, China’s C4ISRT complex has become their schwerpunkt – their center of gravity – that enables them to conduct a range of kinetic and non-kinetic actions throughout the Western Pacific and even globally.
Non-Locality. Hyperobjects are unevenly distributed in time and space and China’s C4ISRT complex is no exception. China’s side of the Taiwan Strait and its outposts in the South China Sea are assessed to have relatively dense concentrations of active and passive sensors, with varying capabilities and quantities of weapons to match. Historically, it has been assumed that as one moves further away from the mainland the fidelity and accuracy of China’s targeting capability drops off.14 However, the last decade of satellite launches have complicated this assessment, as it is no longer clear that a unit’s physical proximity to Chinese-controlled territory corresponds to how accurately that unit can be tracked.15 Still, satellites must either orbit around the Earth or hold a geosynchronous position above it, and as such China’s spy satellites and balloons cannot be everywhere, seeing everything at once—at least not yet.
Non-locality therefore takes on a double meaning. Any interaction an individual unit (such as a U.S. Navy destroyer) has with China’s C4ISRT complex is “local” and this local instance of the C4ISRT complex represents only a fraction of the total system (i.e., you are never interacting with the whole C4ISRT complex at once). Additionally, it is difficult to reliably ascertain the density of sensors at any given point on the map and, therefore it is difficult to be sure one is not being tracked at any given time. China’s increasing deployment of passive, dual-use space-based sensors makes this aspect of non-locality even more pernicious.

Non-human Timescale. China’s C4ISRT complex operates at a non-human timescale in much the same way all modern digital communication systems do. A sensor at the edge of the network can detect a target and report its location, speed and direction back to a fusion center or watchfloor thousands of miles away in tens of seconds. We have become somewhat inured to the speed of digital communications in an age where anyone can place a Zoom call to a family member living on another continent, but this near instantaneous detection speed has real ramifications in a battlespace where the fastest warship can only make 35 knots and an F-35 can only fly at Mach 1.6, still well short of the speed of digital sensor transmission – the speed of light.
Latencies and entropy creep back into C4ISRT systems wherever humans are involved. Double checking or cross checking a “contact” using another sensor can add minutes or more to a targeting process. One goal of China’s “intelligencization” campaign has been to use machine learning tools to speed up sensor data processing, relegating human beings to a secondary, supervisory role in many cases.
Viscosity. The existence of China’s C4ISRT complex certainly seems to have the ability to shape behaviors, particularly among the West’s military and political elites, paralleling the historical debates around nuclear weapons (also a hyperobject) doctrine during the Cold War. At the time of this writing, a debate is raging among American navalists as to whether China’s C4ISRT capabilities, paired with long range precision anti-ship missiles, has rendered U.S. aircraft carriers obsolete. That discussion has even spilled out of professional military circles and into the mainstream, with outlets like Vanity Fair, the Wall Street Journal, and Investor’s Business Daily running articles summarizing the debates.16 In a similar vein, U.S. Indo-Pacific Command (INDOPACOM) leadership has approached Congress about increasing air and missile defenses at Guam.17 Places that once seemed remote from China’s sensors, such as northern Australia’s Air Force bases, are being compelled to reassess their position relative to the C4ISRT hyperobject.18 As the C4ISRT complex grows and evolves, we become more aware of it and it roots itself more firmly in our minds.

An Uneasy Coexistence?
So what should Allied militaries do about the Chinese C4ISRT hyperobject? Here we must diverge significantly from Morton’s ecology-centric understanding of hyperobjects. It is decidedly a philosophical theory, and Morton asserts that the only viable way forward for human philosophy, art, and culture is to attempt to attune ourselves to the hyperobjects now impinging on our world and through this attunement, achieve a form of coexistence. Morton seeks a new type of ecology that is not premised on a “return to nature” rejection of the modern industrial civilization, but a more mature, thoughtful approach that incorporates the reality of hyperobjects into our understanding of the “natural” world.19 This approach leaves the tangible applications wanting.
This, frankly, is not an option for Allied militaries dealing with an adversary C4ISRT hyperobject which is designed to identify, track, and kill them. The Chinese C4ISRT complex is a key enabler for Chinese kinetic and non-kinetic actions. Thus, the ultimate goal of military planning must be to destroy or at least significantly degrade China’s C4ISRT immediately in the event of a conflict and operate effectively in the liminal space before then. Until then, however, a very uneasy coexistence with the hyperobject seems to be our only option. Life did go on after humanity entered the Atomic Age after all. To that end, here are three rules of thumb for practitioners to guide day-to-day interaction with the Chinese C4ISRT hyperobject.
1. There can be no complete picture of the C4ISRT hyperobject. Even if one mapped out all the Chinese land-based sensors, there would still not be a complete picture of the hyperobject. If one added all the orbits and capabilities of the Chinese spy satellites and balloons, one would still not have a complete picture. If one held their breath, dived deep, and sketched the location of all the underwater sensors, one still would not have a complete picture. Even if one added all of the Chinese intelligence and surveillance activities in cyberspace, one still would not have a full picture. Hyperobjects are, by definition, far more than the sum of their parts.
At a minimum, the picture would fail to capture the network connections and the organizational dimension of the data processing, such as the humans working to turn raw data into a holistic understanding of what is happening. Even if one were to somehow add in those dimensions, there would still only be a static snapshot of a complex, dynamic, and constantly evolving system of systems with emergent and potentially chaotic behaviors. The map is not the whole territory, and the inclusion of humans at multiple levels makes the picture even more messy and unpredictable. The emergent behaviors that hyperobjects bring forth cannot be accurately predicted. Despite knowing all the technical capabilities and locations, leaders, engineers, and policymakers simply cannot know or accurately predict how different commanders in China will use them, or how many Chinese actions will drive behaviors in U.S. or allied national security leaders.
We must accept that fact and reorient information and decision-making processes to operate under greater uncertainty, seeking opportunities to experiment and reduce uncertainty. In many respects, the Chinese C4ISRT hyperobject conducted another experiment on the United States with the high-altitude balloon flights, looking for how the U.S. would respond to help them shape their future actions and anticipated responses.
The reality of this systemic dynamism means that discrete, timebound snapshots have to give way to something like simulation or understanding degrees of uncertainty to ever hope to understand how the hyperobject is actually operating at any given time. Today, there are two ways that humans can simulate complex, dynamic behaviors of systems in the world – either by using their own minds or by using a sufficiently powerful computer. Neither of these is perfect, and the flows of data and information to feed that simulation are subject to the same laws of entropy, chaos, and uncertainty as what is trying to be simulated.
Unfortunately, both approaches have limits when it comes to modeling hyperobject behavior. The human mind struggles to grasp something as large, multi-dimensional, and extra-temporal as a hyperobject. Modern computer systems fare better—we are able to model climate change using supercomputers after all—but computer simulations require detailed, up to date, probabilistic data to simulate complex behaviors. The challenge here is that almost every part of the Chinese C4ISRT hyperobject is a tightly-guarded Chinese state secret, including the capabilities of the individual sensor systems, and much of the needed data about individual Chinese behaviors is essentially unknowable. Thus, it is near impossible to feed a computer enough ‘good’ data regularly enough to ensure the computer simulation will be accurate, which itself is a probabilistic concept. And there may be cognitive biases that will hold onto the model even after key Chinese leadership or technical capabilities change.
2. You’ll never be 100% certain if you are being detected (or not). The difficulty of simulating hyperobject behavior with either one’s mind or a computer means that it is very hard to know whether it is collecting information on you, your unit, or your platform at any given time. The C4ISRT hyperobject is perhaps the most elaborate incarnation of Jeremy Bentham’s Panopticon—a theoretical prison structured in such a way that the inmates must assume a warden is watching them, but they can never be sure.20 This superimposition places the target unit in an uncertain state where they must at least double their contingency planning for scenarios in which they are and are not being detected. An avenue for future research would examine the applicability of quantum principles to see if they may provide any assistance in grappling with the duality of Bentham’s Panopticon and its analog with a hyperobject.

This duality may drive commanders and leaders at all levels mad contemplating whether a servicemember’s seemingly random tweet has been observed, collected, and analyzed by the Chinese C4ISRT complex, and what that tweet might compromise about the unit’s readiness, capabilities, or operational security. Even if that does not directly reveal anything, could that tweet provide another one of the thousand grains of sand China needs to effectively target and counter American or allied power?21 Will that new grain of information be used tomorrow, a year from now, a decade from now, or never?
In that light, the daily contact with the hyperobject demands we acknowledge we might be getting collected on at any given time. Thus, we should simply act prudently and strive to minimize the amount of information we leave exposed for the Chinese to find. Practice good operational security. Foster good relationships with domestic intelligence and law enforcement services to understand the area threat. Strive to become a harder and more unpredictable target, whether one is a deckplate sailor on a destroyer, a defense contractor, Congressional staffer, or the Secretary of Defense.
3. Finally, a hyperobject is not easily reducible to its constituent parts. Our inability to reliably map out the hyperobject’s shape or model its behavior also impacts our ability to identify key points of strength or weakness within the system and to understand how disabling or destroying one part will affect the performance of the whole. Practitioners must resist the temptation to assume that knowledge of constituent parts yields knowledge of the whole. Understanding the technical specifics of a Chinese ISR satellite or balloon does not mean that you understand the overall behavior of how Southern Command will utilize them, which may be different from Eastern Command’s approach, which may be different from the global or meta-level behavior of the hyperobject—the effect of non-human time scales, viscosity, scale, and non-locality.
Military leaders in particular are best equipped to grapple with this rule of thumb. Military leaders train against adversary orders of battle and seek to create overmatch conditions for tactical victories. But at the strategic level, the familiar treatises of Sun Tzu and Carl von Clausewitz provide surprisingly sage advice for dealing with the irreducibility of the Chinese C4ISRT hyperobject. Sun Tzu detailed the challenges; ephemerality, and general uncertainty of warfare, and how actions by one side’s leadership might create unpredictable behaviors from the enemy. Clausewitz spoke of the centers of gravity, the paradoxical trinity of emotion, chance, and reason, and principles—not laws—of war. These theorists understood that all the knowledge could not dictate the outcomes and that the friction or fog of war meant warfighters had to operate to clear the fog and reduce the uncertainty to be prepared for the unexpected.
Today, we must reacquaint ourselves with these concepts with a view toward how we might understand the uncertainty of the Chinese C4ISRT hyperobject. It will always be in some corner of our minds. We must accept that we will never fully know and be able to predict its actions. Seek opportunities to test their system to see how they respond—does Southern Command respond the same as Eastern Command to the same event? How does China respond to a notable cyber breach of a state-owned enterprise compared to economic sanctions against the same enterprise? These types of tests help leaders at all levels better understand the hyperobject and modifies their behaviors from determinism to probabilities.
The End of the World?
Perceptive readers may have noted the subtitle of Morton’s book “Philosophy and Ecology After the End of the World.” The end of the world alluded to here is more prosaic than it first appears. Morton is not talking about the apocalyptic climax of all human events. Instead, he highlights the ability of hyperobjects to destroy—or at least severely alter—the small, local, and temporal mental ‘worlds’ that humans inhabit on a day-to-day basis. Once one is made aware of a hyperobject, its viscosity ensures it will stick in your mind, altering the way you think about the world, or at least requiring a Herculean mental effort to deny its existence.22
Morton points out how discussing the weather with a stranger has historically been considered a safe, albeit boring, way to pass the time.23 Our contemporary understanding of climate change has altered the experience of ‘talking about the weather.’ Weather is revealed to just be a localized experience of the climate overall, which means talking about the weather risks you bringing up the topic of climate change with a stranger. The hyperobject of climate change has intruded into the normal conversation about the weather, turning the whole experience into a fraught social tightrope.24 The little world of the boring weather conversation has been forever changed.
Decades of Chinese investment in sensors, networks and data management means that Allied operations in the Western Pacific are now occurring within a dynamic, complex, shifting, and expanding Chinese C4ISRT ecosystem. The national security community should heed Morton’s hyperobjects and how they provide a better framework for understanding the reality-altering nature of the Chinese C4ISRT complex as a hyperobject. The exact extent and scale of the hyperobject is difficult to ascertain, thereby making it hard to say definitively whether one is being tracked by it at any given time, particularly during this uneasy period of great power competition. Through decades of hard work and investment, China created this hyperobject, and by doing so, it has changed the long-range surveillance and targeting game.
Has knowledge of the Chinese C4ISRT hyperobject altered the worlds of the U.S. destroyer captain, the Australian F/A-18 pilot, or the INDOPACOM command team? Arguably yes, but probably not as explicitly as it should have. The carrier debate in the U.S. indicates we are likely in the early phase of understanding the impact of the C4ISRT hyperobject crashing into the rigidly structured world of the U.S. Navy’s 30-year shipbuilding plan and the DoD’s anachronistic acquisition system. These disruptions to our preferred way of doing things are likely to increase in frequency and intensity over the coming decade, putting a premium on our ability to understand and adapt to a hyperobject dominated battlespace. Practitioners would do well to reflect on what they actually know about the Chinese C4ISRT hyperobject—and more broadly, what can be known—to better understand how it influences their daily actions. From there, leaders can begin to respond in kind. Until then though, the Western response will be suboptimal at best, or catastrophically misinformed at worst.
Lieutenant Commander Shane Halton is an intelligence officer currently serving in California. He has previously served on exchange with the Royal Australian Navy and as a requirements officer at the Navy’s Digital Warfare Office.
Lieutenant Commander Ryan Hilger is a Navy Engineering Duty Officer stationed in Florida. He has served onboard USS Maine (SSBN 741), as Chief Engineer of USS Springfield (SSN 761), and ashore at the CNO Strategic Studies Group XXXIII and OPNAV N97. He holds a Masters Degree in Mechanical Engineering from the Naval Postgraduate School and is a doctoral student in systems engineering at Colorado State University.
These views are presented in a personal capacity and do not necessarily represent the official views or policies of the Department of Defense or the Department of the Navy.
References
1. Helene Cooper, “Pentagon Says it Detected a Chinese Spy Balloon Hovering Over Montana,” The New York Times, February 2, 2023, https://www.nytimes.com/2023/02/02/us/politics/china-spy-balloon-pentagon.html
2. Ibid.
3. Katie Bo Lillis, Jeremy Herb, Josh Campbell, Zachery Cohen, Kylie Atwood, and Natasha Bertrand, “Spy balloon part of broader Chinese military surveillance operation, US intel sources say,” CNN, February 8, 2023, https://www.cnn.com/2023/02/07/politics/spy-balloon/index.html
4. Bob Hall, “Chinese spy balloon exposes US vulnerability to EMP attacks,” Washington Examiner, February 13, 2023, https://www.washingtonexaminer.com/restoring-america/courage-strength-optimism/chinese-spy-balloon-exposes-us-vulnerability-to-emp-attacks
5. Michael Mazza, “The Chiense spy balloon is a tangible Sputnik moment for Biden and Americans,” New York Post, February 6, 2023, https://nypost.com/2023/02/06/the-chinese-spy-balloon-is-a-tangible-sputnik-moment-for-biden-and-americans/
6. “In Their Own Words: China’s National Defense in the New Era,” Chinese Aerospace Studies Institute, Air University, July 2019, https://www.airuniversity.af.edu/Portals/10/CASI/documents/Translations/2019-07%20PRC%20White%20Paper%20on%20National%20Defense%20in%20the%20New%20Era.pdf?ver=akpbGkO5ogbDPPbflQkb5A%3d%3d
7. James S. Johnson, “China’s vision of the future network-centric battlefield: Cyber, space and electromagnetic asymmetric challenges to the United States,” Comparative Strategy, Volume 37, Issue 5 (March 2019): 373-390, https://www.tandfonline.com/doi/full/10.1080/01495933.2018.1526563
8. Timothy Morton, Hyperobjects: Philosophy and Ecology after the End of the World (Minneapolis, MN: University of Minnesota Press, 2013).
9. Morton, “Hyperobjects,” 2.
10. Morton, “Hyperobjects,” 1.
11. Johnson, “China’s Vision of the Future Network-Centric Battlefield,” 373-390; Thomas R. McCabe, “Chinese Intelligence, Surveillance, and Reconnaissance Systems,” Journal of Indo-Pacific Affairs (Spring 2021): 1-6, https://media.defense.gov/2021/Mar/07/2002595026/-1/-1/1/25%20MCCABE.PDF.
12. Ziyu Zhang, “China’s military structure: what are the theatre commands and service branches?,” South China Morning Post, August 15, 2021, https://www.scmp.com/news/china/military/article/3144921/chinas-military-structure-what-are-theatre-commands-and-service
13. Michael S. Chase and Jeffrey Engstrom, “China’s Military Reforms: An Optimistic Take,” Joint Forces Quarterly 83, Fourth Quarter (2016): 49-52, https://apps.dtic.mil/sti/pdfs/AD1020041.pdf.
14. “The odds on a conflict between the great powers,” The Economist, January 25, 2018, https://www.economist.com/special-report/2018/01/25/the-odds-on-a-conflict-between-the-great-powers.
15. McCabe, “Chinese Intelligence, Surveillance, and Reconnaissance Systems,” 1-6.
16. Marc Wortman, ““Floating Pointlessness”: Is This the End of the Age of the Aircraft Carrier?,” Vanity Fair, May 5, 2022, https://www.vanityfair.com/news/2022/05/is-this-the-end-of-the-age-of-the-aircraft-carrier;
“The Navy’s Big Carrier Groups Are Sitting Ducks,” Wall Street Journal, April 14, 2022, https://www.wsj.com/articles/navy-aircraft-carrier-fleet-battle-group-target-warfare-china-missile-asbm-11649885333;
Gillian Rich, “This Icon Of U.S. Power Is More Sinkable Than Ever But Hard To Kill Off,” Investor’s Business Daily, January 31, 2020, https://www.investors.com/news/aircraft-carriers-more-sinkable-but-hard-to-kill-off/.
17. C. Todd Lopez, “Time for Guam Missile Defense Build-Up Is Now,” U.S. Indo-Pacific Command, December 9, 2021, https://www.pacom.mil/Media/News/News-Article-View/Article/2867950/time-for-guam-missile-defense-build-up-is-now/
18. Malcolm Davis, “Australia must prepare as China’s coercive capabilities draw closer,” Australia Strategic Policy Institute, September 15, 2021, https://www.aspistrategist.org.au/australia-must-prepare-as-chinas-coercive-capabilities-draw-closer/
19. Morton, “Hyperobjects,” 201.
20. University College London, “The Panopticon,” accessed July 9, 2022, https://www.ucl.ac.uk/bentham-project/who-was-jeremy-bentham/panopticon
21. Vernon Loeb and Walter Pincus, “China Prefers the Sand to the Moles,” Washington Post, December 12, 1999, https://www.washingtonpost.com/wp-srv/WPcap/1999-12/12/097r-121299-idx.html
22. Morton, “Hyperobjects,” 35.
23. Morton, “Hyperobjects,” 100-104.
24. Elizabeth Boulton, “Climate change as a ‘hyperobject’:a critical review of Timothy Morton’s reframing narrative,” WIRE Climate Change (2016), https://www.researchgate.net/profile/Elizabeth-Boulton-3/publication/303801414_Climate_change_as_a_’hyperobject’_a_critical_review_of_Timothy_Morton’s_reframing_narrative_Climate_change_as_a_hyperobject/links/5dd5110f458515cd48ac6dfe/Climate-change-as-a-hyperobject-a-critical-review-of-Timothy-Mortons-reframing-narrative-Climate-change-as-a-hyperobject.pdf
Featured Image: A U.S. Air Force U-2 pilot looks down at the Chinese surveillance balloon as it hovers over the U.S. on Feb. 3. (Department of Defense photo)

