We Won but We Failed: What We Should Learn
In Andromeda Strain, the scientists of the Wildfire Team struggled against their pathogen foe, (spoiler alert) only to have their problems solved by circumstance and environment. An entire plot was written about a crisis team that, in the end, accomplished nothing. East African piracy, while by no means eradicated, looks perhaps to have peaked, and public interest waning possibly even faster. Sure, the Maersk Texas was attacked in May, but this single blip on the radar is a paltry show compared to the still-notable number of small-boat attacks off the coast of India, yacht abductions, and beach resort kidnappings.
Unfortunately, after almost a decade of engagement, the West’s maritime Wildfire team has had almost no hand in the changes on the high seas. A series of military incursions by neighbors, newfound vigor in the AU mission, and rise of PMC’s at sea have changed the state of play and cut the mission short, leaving a real possibility for naval leadership to miss the lessons learned from their recent miscalculations.
As the counter-piracy mission is fresh in our minds and before the threat fades into the jaws of vengeful regional militaries, we should use the opportunity to recognize and assess our failures as a force in countering piracy on the high seas.
The West Reacts to the Pathogen
In scope, the naval response to the threat of piracy appeared robust. Dozens of warships plied the waters in search of high-seas bandits. Area patrols ran alongside convoy escorts. Several multi-national coalitions (NATO, U.S.-led Combined Military Forces, the EU) ran operations concurrently with the independent efforts of ten or more countries at any one time. The Indian navy recently captured a stunning 61 pirates after a pitched gun battle. Over 20 nations now meet for the annual Shared Awareness and Deconfliction (SHADE) conference to build a united front against piracy. Maritime Patrol Aircraft and UAVs from multiple nations surveil the Internationally Recommended Transit Corridor (IRTC), pirate anchorages, and the open ocean. There was a reasonable expectation that such a massive military drag net might stymie piracy. However, the result was a better skilled and better organized pirate. As Napoleon said, “You must not fight too often with one enemy, or you will teach him all your art of war.”
Piracy’s Adaptation and Resistance
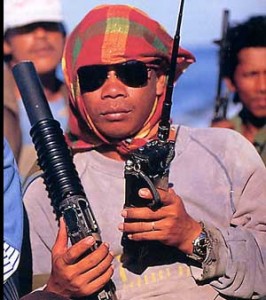
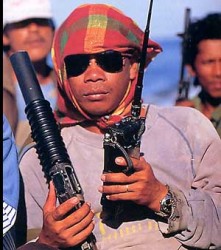
Until military action ashore cut short the party, coastal raids with small skiffs developed into multi-million dollar kidnapping operations with captured tankers converted to motherships. Pirates used UHF communications, skilled hostage negotiators, and money changers in Dubai. Merchants deactivated their automatic identification system (AIS), a system used for vessel safety during the height of piracy around the Straits of Malacca, as pirates at large used it as a homing beacon. Pirates adapted to the law-enforcement rules of engagement used by the respective patrolling navies, hiding or disposing of all pirate paraphernalia and making it next-to-impossible for maritime enforcers to get the convictions occasionally sought. Many pirates moved to new areas altogether, shifting operations away from patrols and avoiding the range of immediate military responses.
The focus of piracy shifted from capturing cargo to capturing people. Kidnapping was the name of the game. Due to an inability to enforce arrangements, some companies paid full ransom for captured employees and only received a fraction of their personnel in return. EUNAVFOR even reported more brazen tactics of avoiding capture, namely the threatened and actual torture of hostages.
This adaptation, combined with the lack of political stability, created threats beyond endangering global commerce. With Al-Qaeda operating in Somalia next to Al-Shabab, endless opportunities presented themselves for terrorist networks to simply generate profits through partnership or create havoc with vessels purchased from pirates. Rather than siphon off fuel for profits, the pirates could sell a vessel wholesale to terrorists who could use the vessel as a massive explosive in a civilian port, blockage in the mouth of a harbor, or a suicide battering ram against an unsuspecting warship. Capture-and-switch tactics with maritime commercial vehicles had precedent; the 1998 hijacking of the Petro Ranger being a case in point. It only takes a savvy pirate with the right connections to profit from the sale of hijacked tankers for acts of terrorism. Piracy is a crime of opportunity, and human beings are always good at finding new ones.
Breaking the Sea-Shore Learning Cycle
The key to breaking the adaptation puzzle is to boost the intensity of the counter-piracy dosage. One can have the best weapons in the world, but it won’t matter unless the operational concept is correct. The U.S. was weak on piracy, an inch-deep mile-wide river. Pirates waded easily across to tell their compatriots what they’d seen, creating a deadly sea-to-shore innovation cycle that improved pirate learning. This must be solved through more vigorous piracy prosecution, more aggressive rules of engagement (ROE)/posture, and a shore kinetic solution.
Instead, the U.S. released many captured pirates back into Somalia, only prosecuting those that attacked the rare U.S. flagged vessel. The idea behind this policy is that piracy is a crime, not a national security issue. If the vessel’s flag would not prosecute, there could be no trial or detention. Piracy is however very much a national security issue – not only does it drive up the cost of shipping and goods, but pulls mission-ready forces from other duties to keep the costs from rising higher. Sailors deployed to counter-piracy missions can attest to lengthy force protection details off the coast during RHIB transfers of detainees to shore. These temporary detentions were a waste of time and money, punishing piracy with nothing more than a few days in the ship’s center-line passageway with three squares meals and regular washes. The idea that pirates “learned” something from their capture was correct. The lesson was that they likely would survive encounters with U.S. warships and be returned to their anchorages. At the very least, more suspected vessels should have been diverted and escorted to ports where their hulls, cargo, and crew could be inspected and held if necessary. U.S. tactics involving capture had little meaning without a resolution other than emancipation. At worst, such impotent gestures actively undermined the authority of the U.S. presence.
Actions Louder than Words
These operations would have been aided by more lenient ROE and a higher level of aggressiveness in the U.S. posture toward piracy. This is a complicated subject as the rules were designed to maximize legitimacy and minimize controversy and liability. It is frustrating to read message traffic insisting on defining pirates clearly caught in the act as “suspected.” Pirates, when positively identified, are hailed and warned, but rarely destroyed. A comical irony is that an escort for a pirated vessel provides, if anything, little more than military protection for the pirates on the vessel.
Better ROE would be more aggressive, allowing the engagement and destruction of vessels with known associations to piracy. Once the chance to surrender is given, threats must be made good. To counter the use of human shields, a counter-offer must be made to pirates. The normal method, as I witnessed it, is that U.S. warships hail pirate vessels, occasionally fire warning shots, then are deterred by the presence of human shields or pirate threats to kill their hostages.
Ending Incentivization
Just as the U.S. has a standing policy not to negotiate with terrorists, the same should be clearly applied to pirates: remove the incentive to use hostages. Piracy is not about ideologies, but competing costs and benefits. The U.S. concept of operations places far too much stake on the presence of hostages, further imperiling mariners by encouraging their capture. Military policy should make hostage-taking and the use of human shields a non-factor. If uncooperative, all pirate vessels should be engaged with disabling or destructive fire. Rather than reducing the equation to capture or an escape with hostages, warships should amend the options: capture or death. If hostages are used as shields or threatened with death, the pirates should understand that they only further endanger their own lives by risking lethal retaliation. If hostages are killed by pirates, the responsibility lies with the pirates, not with the military endeavoring to save them. This is an unpleasant idea, but kinetic operations of this kind can rarely be conducted without at least a trace of regrettable collateral damage. Military planners should recognize this unfortunate inevitability and pursue the larger goal of protecting future mariners and an entire region’s stability.
Not Just the Sea
One development that did prove effective was stationing warships at pirate anchorages. This led to a better picture of piracy operations, their frequency, and capabilities. However, partially due to the presence of hostages, the infrastructure remained largely undisturbed. From only a few miles off the coast, a swath of defenseless pirate infrastructure was often in view of my own vessel. I remember SUVs brazenly shadowing us along the shore as we maneuvered close to the land. Small vessels were clearly visible transiting to and from shore with supplies for anchored pirated vessels. Pirate skiffs were propped up in clusters above the tide near supply shacks and rows of vehicles. Pirates came to rely on these facilities to coordinate their operations at sea while simultaneously maintaining a large stable of captured vessels and hostages. With rare exception, these shores were left alone, covered in equipment ripe for destruction. Again, military leaders were naturally worried about hostage collateral damage. Yet naval gunfire can be used to great effect against safe targets at pirate anchorages. UHF towers, clusters of empty vehicles, supply vessels, unattended skiffs, and the assorted support facilities onshore are all easy targets for naval gunfire. This is not only less expensive than leaving the pirates alone, launching 1.5 million dollar Tomahawks, or drone strikes, but terrifying for pirates realizing they could be bombarded at any moment with a ship offshore. This scorched-earth policy for pirate shore facilities should be common practice.
You’re Gonna Need a Bigger (and smaller) Boat
America’s military counter-piracy medication comes in the form of ships-of-the-line, namely DDGs and a few FFGs. While versatile craft, these are inherently conventional, centralized combatants designed for confrontations with modern navies. They are expensive, complicated blue-water craft weighed down with anti-submarine, anti-surface, and anti-air capabilities unsuited for the task of counter-piracy. VLS, AEGIS, torpedoes, Harpoon, towed arrays, sonobuoys, etc. have little to no use here. These platforms have a limited aviation capability and little room for detainees caught while on patrol. There are even FFGs deployed to Somalia without helicopters, making them next to useless when it comes to responding to calls for help outside of 20nm. Additionally, unlike the conventional warfare areas, there is no formal training regimen for these ships that deals with piracy specifically, their assigned mission.
Amphibious platforms, on the other hand, have the supplies and space to contain detainees for long periods without impacting crew effectiveness. Amphibious platforms also bring vital improved air assets/compatible flexibility not sufficiently present in CRUDES. The USS Oak Hill’s certification to carry riverine boats last summer demonstrates amphibious ships’ versatility with the ability to deploy patrol boats in concert with multiple air assets. Rather than a single ship and helicopter covering hundreds of miles of coastline, a whole swarm of air and sea assets, bolstered by a large detainee space and afloat support facility, become available in a single platform. These kinds of coastal patrol operations were executed to great effect during Vietnam using Landing Ship Tank (LST) vessels as bases to deploy Patrol Boats-Riverine (PBRs) and helicopters. A similar concept would be a far more effective counter-piracy force structure off Somalia.
Andromeda Strain: Not Walking Away Empty Handed
As regional entities take turns carving out pieces of the vacuum in which pirates operated, we will naturally let out a sigh of relief and enjoy a chance to walk away from the piracy issue. We must not, however, allow our efforts to be for naught; we must at a minimum take with us the important lessons from our failed efforts. Piracy is a crime of opportunity. It can only be deterred by changing the cost-benefit analysis and removing the chances to commit the crime. The United States’ incomplete capture strategy, backed up by weak actions/ROE, only taught pirates that, with a little innovation, the usual result of a run in with an American vessel was a free ride home.
Matt Hipple is a surface warfare officer in the U.S. Navy. The opinions and views expressed in this post are his alone and are presented in his personal capacity. They do not necessarily represent the views of U.S. Department of Defense or the U.S. Navy.

I have to agree with the overall premise here, Somali piracy was never really a maritime issue at its source and wasn’t going to be defeated by a naval effort, it was a seaward expansion of the warlordism that been a way of life in Somalia since at least the early 90s. The only group with real success at stopping piracy was the Islamic Courts Union, who shut it down when they controlled southern Somalia for most of 2006. Piracy came back when the Ethiopians invaded and forced them out of Mogadishu and the pirate strongholds at the end of that year.
I do have to disagree with a few points:
– Has it ever been proven that the pirates ever used AIS (or other technical means) to pick or locate their targets?
– While things do seem to be on an upswing in terms of the AMISOM/Kenyan campaign against Al Shabab, there are still lots of hostages being held by pirates…178 hostages on 12 ships as of mid-June (http://www.icc-ccs.org/piracy-reporting-centre/piracynewsafigures ). The US has responded with force when US ships/persons were attacked by pirates…but to date that’s only been 2 incidents (MAERSK ALABAMA and the QUEST).
I totally agree on the mission not being truly at sea. The original article was written last year assuming that Somalia WOULDN’T get tag-teamed by all it’s neighbors and it’s conclusion was essentially yours. I’m a big fan of the political “divide and conquer” strategy, namely changing US policy to allow explicitly for a divided Somalia. That would make stabilization easier, with the smaller political units feeling secure in their position. That all said, our maritime mission could have been FAR more effective than it was.
-I won’t say it’s been proven, but I observed everyone doing it and I can only assume that would be the reason. No doubt these pirates were able to steal some of these systems off ships they have captured.
– Yes, they still have the remnants of more halcyon days of piracy, but I’d say that is a surplus from a bygone time. The fact we only harass pirates to the full measure that attack US flagged ships was part of the problem. Our authority was being flaunted every time we dropped pirates back off near their anchorages. They sent cars alongshore to pick them up!
Informative piece just came out yesterday from SomliaReport with pirate sources on why operations have dried up lately: mostly weather, lack of success (breaking the investment/business cycle), pressure from the EU near Kisamayo, and pressure from the Puntland Marine Police Force:
http://www.somaliareport.com/index.php/post/3453/Pirates_Feel_the_Pinch
Matt, loosened ROE might also result in a press/IO debacle with civilians killed in a confusing firefight. The simple cost-benefit analysis right now comes up high on cost and almost zero benefit–little to no US national interests are at stake. So why risk the blood of one US sailor?
john
The issue is long-term incentivization. If we allow hostages to “work” for pirates, then pirates will seek more hostages. We must mitigate risk to the hostages where we can, but giving pirates increased agency due to the presence of hostages merely gives pirates more reason to get hostages. We need to create a Pavlovian response that will make pirates shy from such operations.
Matt
Interesting piece. I enjoyed the part about the pirate learning/innovation cycle. However, I’ve gotta agree with John about the reality of a more aggressive approach against the pirates. Specifically, your statement that “If hostages are used as shields or threatened with death, the pirates should understand that they only further endanger their own lives by risking lethal retaliation.” seems a bit of an over-simplified solution. The only way to get at a pirate threatening a hostage or using one as a human shield might be to shoot through the hostage. In many cases there’s not enough time at sea to mount an effective effort to free the hostages while realistically minimizing the threat to the hostages before they’re moved ashore. Even if there is, the preferences of the offended country, the shipping company, and possibly even the hostages might prefer a negotiated end to the possibility of bloodshed. The U.S. acting unilaterally in such instance would produce the sort of IO fiasco John mentioned. Getting more aggressive after pirates who take one’s own countrymen hostage is more do-able, but even then raids ashore risk raising the stakes for the others in pirates’ hands: http://www.warisboring.com/2012/06/19/warships-international-fleet-review-seals-raise-the-stakes/
In such a case a complete follow-up by seeking and bringing those who harm one’s nationals to justice is warranted, but such a case is rare.
Scott