Distributed Lethality Topic Week
By LCDR Chuck Hall and LCDR David T. Spalding
The U.S. Navy’s Surface Force is undergoing a cultural shift. Known as “Distributed Lethality,” this strategy calls for our naval combatants to seize the initiative, operate in dispersed formations known as “hunter-killer” surface action groups (SAG), and employ naval combat power in a more offensive manner. After years of enjoying maritime dominance and focusing on power projection ashore, the U.S. Navy is now planning to face a peer competitor in an Anti-Access/Area Denial (A2AD) environment. Long overdue, Distributed Lethality shifts the focus to one priority – warfighting. Far from a surface warfare problem alone, achieving victory against a peer enemy in an A2AD environment will require leveraging all aspects of naval warfare, including naval cryptology.
[otw_shortcode_button href=”https://cimsec.org/buying-cimsec-war-bonds/18115″ size=”medium” icon_position=”right” shape=”round” color_class=”otw-blue”]Donate to CIMSEC![/otw_shortcode_button]
Naval Cryptology has a long, proud history of supporting and enabling the Fleet. From the Battle of Midway in 1942, to leading the Navy’s current efforts in cyberspace, the community’s expertise in SIGINT, Cyber Operations, and Electronic Warfare is increasingly relevant in an A2AD environment. Led by Commander, U.S. Fleet Cyber Command/U.S. TENTH Fleet, the community is comprised of officers and enlisted personnel serving afloat and ashore and who are well integrated with the Fleet, intelligence community, and U.S. Cyber Command. Given its past history and current mission sets, naval cryptology is poised to enable distributed lethality by providing battlespace awareness, targeting support, and effects, in and through the electromagnetic spectrum and cyberspace.
Battlespace Awareness
Battlespace Awareness, as defined in the Information Dominance Roadmap, 2013-2028, is “the ability to understand the disposition and intentions of potential adversaries as well as the characteristics and conditions of the operational environment.” It also includes the “capacity, capability, and status” of friendly and neutral forces and is most typically displayed as a Common Operating Picture (COP). To be effective, however, battlespace awareness must seek to provide much more than just a COP. It must also include a penetrating knowledge and understanding of the enemy and environment — the end-user of which is the operational commander. The operational commander must be able to rely on predictive analysis of enemy action in the operational domain to successfully employ naval combat power in an A2AD environment.
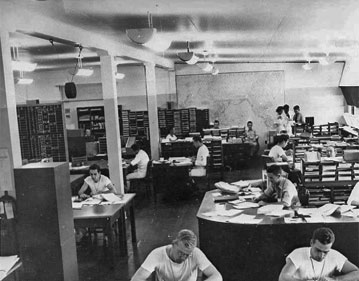
Naval Cryptology has historically provided battlespace awareness through the execution of Signals Intelligence (SIGINT) operations. During World War II, Station HYPO, located in Pearl Harbor and headed by Commander Joseph Rochefort, collected and decrypted the Japanese naval code, known as JN-25. Station HYPO’s exploitation of Japanese naval communications was sufficient to provide daily intelligence reports and assessments of Japanese force dispositions and intentions. These reports were provided to naval operational commanders, to include Admiral Chester W. Nimitz, Commander in Chief, U.S. Pacific Fleet and Commander in Chief, Pacific Ocean Areas. On May 13, 1942, navy operators intercepted a Japanese message directing a logistics ship to load cargo and join an operation headed to “Affirm Fox” or “AF.” Linguists from Station HYPO had equated “AF” to Midway in March after the Japanese seaplane attack on Hawaii (Carlson, 308) and was thus able to confirm Midway as the objective of the upcoming Japanese naval operation. Station HYPO was also able to give Nimitz the time and location of the Japanese attack point: 315 degrees, 50 nm from Midway, commencing at 7:00AM (Carlson, 352). This allowed Nimitz to position his forces at the right place, designated Point Luck, northeast of Midway, placing the U.S. fleet on the flank of the Japanese (Carlson, 354). Had Station HYPO’s efforts failed to provide this battlespace awareness, Admiral Nimitz would not have had enough time to thwart what might have been a surprise Japanese attack.
Victory at Midway was founded on the operational commander’s knowledge of the enemy’s force construct and disposition. Currently the product of both active and passive, organic and non-organic sensors, achieving battlespace awareness in an A2AD environment will require more emphasis on passive and non-organic sensors, and increased national-tactical integration in order to prevent detection and maintain the initiative. The “hunter-killer” SAGs will be entirely dependent upon an accurate and timely COP – not just of enemy forces, but of dispersed friendly forces as well. Just as battlespace awareness enabled triumph against the Imperial Japanese Navy, so too will it be the very foundation upon which the success of distributed lethality rests. Without it, the operational commander cannot effectively, and lethally, disperse his forces over time and space.
Targeting Support
Another key enabler of the Surface Navy’s shift to the offensive will be accurate and timely targeting support. Though support to targeting can come in many forms, as used here it refers to the triangulation and precision geolocation of adversary targets via communications intelligence and radio direction finding (RDF). In an environment in which options to “fix” the enemy via radar or other active means introduces more risk than gain, RDF presents itself as a more viable option. Indeed, the passive nature of direction finding/precision geolocation makes it particularly well suited for stealthy, offensive operations in an A2AD environment. Leveraging both organic and non-organic sensors in a fully integrated manner — RDF will provide “hunter-killer” SAG commanders with passive, real-time, targeting data.
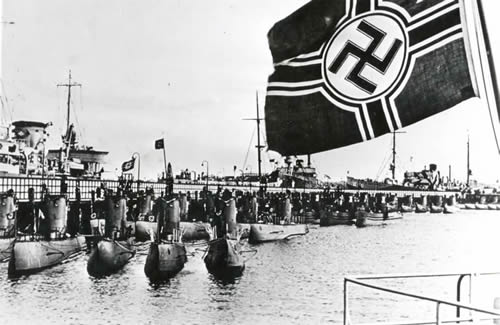
Perhaps one of the best historical examples of Naval Cryptology’s support to targeting can be seen in the Battle of the Atlantic. The Third Reich had threatened the very lifeline of the war in Europe as Admiral Donitz’ U-boats were wreaking havoc on Allied merchant vessels throughout the war. Though America had begun intercepting and mapping German naval communications and networks as early as 1938, it was not as critical then as it was upon entry into the war. By the time America entered the war, the U.S. Navy’s SIGINT and cryptanalysis group, OP-20-G, boasted near 100 percent coverage of German naval circuits. Many of these circuits were used for high frequency (HF), long range shore-ship, ship-shore, and ship-ship communications. The ability to both intercept these communications and to locate their source would be necessary to counter the Axis’ attack. That ability was realized in an ever growing high frequency direction finding (HFDF) network.
The HFDF network originally consisted of only a handful of shore stations along the Atlantic periphery. Throughout the course of the war it grew to a rather robust network comprised of U.S., British, and Canadian shore-based and shipborne systems. The first station to intercept a German naval transmission would alert all other stations simultaneously via an established “tip-off” system. Each station would then generate a line of bearing, the aggregate of which formed an ellipse around the location of the target. This rudimentary geolocation of German U-boats helped to vector offensive patrols and enable attack by Allied forces — thus taking the offensive in what had previously been a strictly defensive game. The hunter had become the hunted.
Enabling the effectiveness of increased offensive firepower will require more than battlespace awareness and indications and warning. Going forward, Naval cryptologists must be agile in the support they provide — quickly shifting from exploiting and analyzing the enemy, at the operational level, to finding and fixing the enemy at the tactical level. Completing the “find” and “fix” steps in the targeting process will enable the “hunter-killer” SAGs to accomplish the “finish.”
Cyber Effects
Finally, cyber. Receiving just a single mention, the original distributed lethality article in Proceedings Magazine refers to the cyber realm as, “the newest and, in many ways most dynamic and daunting, levels of the battlespace—one that the Surface Navy, not to mention the U.S. military at large—must get out in front of, as our potential adversaries are most certainly trying to do.” Indeed, the incredible connectivity that ships at sea enjoy today introduces a potentially lucrative vulnerability, for both friendly forces and the adversary. Similar to battlespace awareness and targeting, Naval Cryptology has history, albeit limited, in cyberspace. Cryptologic Technicians have long been involved in Computer Network Exploitation (CNE) and the Navy was the first service to designate an enlisted specialty (CTN) in the cyber field. According to the FCC/C10F strategy, not only do they, “operate and defend the Navy’s networks,” but they also, “plan and direct operations for a subset of USCYBERCOM’s Cyber Mission Forces.” The combination of history and experience in cyberspace, coupled with the FCC/C10F designation as the Navy’s lead cyber element, clearly places the onus on naval cryptology. As the Navy seeks to protect its own cyber vulnerabilities, and exploit those of the adversary, the execution of effective cyber operations by the cryptologic community will be critical in enabling distributed lethality.
Going Forward
Today, through a wide array of networked, passive, non-organic sensors, and integration with national intelligence agencies and U.S. Cyber Command, naval cryptology is well-positioned to enable distributed lethality by providing battlespace awareness, targeting support, and effects, in and through the electromagnetic spectrum and cyberspace. Yet, similar to the surface force, a cultural shift in the cryptologic community will be required. First, we must optimize national-tactical integration and better leverage and integrate off-board sensors. The uniqueness of the A2AD environment demands the integration and optimization of passive, organic and non-organic sensors in order to prevent counter-targeting. Second, we must prioritize the employment of direction finding and geolocation systems, ensuring they are accurate and sufficiently integrated to provide timely targeting data for weapons systems. This will require a shift in mindset as well, from simple exploitation to a focus on “find, fix.” Third, we must continue to lead in cyberspace, ensuring cyber defense in depth to our ships at sea while developing effects that effectively exploit adversary cyber vulnerabilities. Finally, naval cryptology’s role in distributed lethality cannot occur in a vacuum — increased integration with the Fleet will be an absolute necessity.
Distributed lethality is the future of Naval Surface Warfare — a future in which the cryptologic community has a significant role. In order to ensure the Surface Force can seize the initiative, operate in dispersed formations known as “hunter-killer” SAGs, and employ naval combat power in a more offensive manner in an A2AD environment, Naval Cryptology must stand ready to provide battlespace awareness, targeting support, and effects, in and through the electromagnetic spectrum and cyberspace.
LCDR Chuck Hall is an active duty 1810 with more than 27 years of enlisted and commissioned service. The opinions expressed here are his own.
LCDR David T. Spalding is a former Cryptologic Technician Interpretive. He was commissioned in 2004 as a Special Duty Officer Cryptology (Information Warfare/1810). The opinions expressed here are his own.
[otw_shortcode_button href=”https://cimsec.org/buying-cimsec-war-bonds/18115″ size=”medium” icon_position=”right” shape=”round” color_class=”otw-blue”]Donate to CIMSEC![/otw_shortcode_button]
Works cited:
Ballard, Robert. Return to Midway. Washington, D.C: National Geographic, 1999.
Parshall, Jonathan. Shattered Sword : The Japanese Story of the Battle of Midway. Dulles, Va. Poole: Potomac Chris Lloyd distributor, 2007.
Carlson, Elliot. Joe Rochefort’s War: the Odyssey of the Codebreaker Who Outwitted Yamamoto at Midway. Annapolis, MD: Naval Institute, 2011. Print.


Well done, gentlemen. So many contemporary cryptologists are afraid to comment in the open (or even collateral forums) on what is well-established history and commonly understood, yet unclassified tactical capabilities. There is a reason operators tend to ignore them. You are adding value to the discussion on this important topic.
Thanks, Chris.
These objectives are sound; however, they have not been endorsed and implemented for the Surface Navy for several reasons:
a) Ignorance of value of cryptologic information. Information from organic and offboard cryptologic (SIGINT) systems is compartmented to protect sources and methods. Within the surface navy access to this information is limited; and, its potential for application in tactical operations is not well understood and appreciated. Therefore, the surface community has little incentive to press for the integration/fusion of this information with ownship/force information in the ship’s combat system.
b) Ill Defined Strategy. The Navy Strategy for Information Dominance 2013-2027 states:
“The Information Dominance pillar can be our most powerful asset, or it can be our greatest liability. If we integrate it intelligently, and if we execute it correctly, we will be able to seize the operational initiative, gain tactical advantage, and win future battles with overwhelming speed.”
“Integrate all-source information across kill chains”.
“Disparate information sources will necessarily span physical locations, security classifications and Navy warfighting domains, but they must be synthesized to create actionable knowledge.”
The Strategy doesn’t indicate whether this synthesis/integration will occur, ashore or on ship. It does not acknowledge that this integration of ownship and offboard information has to occur onboard ship when the force is operating in EMCON against a near peer adversary.
b) Absence of up-to-date Navy Command and Control Concept. Submarine operations are characterized by independent operations in silence. Given these imperatives, access to and integration of offboard information has been addressed in the context of over-the-horizon targeting since the 1970s-1980s. In contrast, surface navy command decisions at the tactical level are made by the Composite Warfare Commander (CWC) and his/her principal warfare commanders. Under the CWC concept, the Officer in Tactical Command (OTC) delegates command authority in particular warfare areas to subordinate commanders within the CWC organization including: Sea Combat Commander (SCC), Surface Warfare Commander (SUWC), Undersea Warfare Commander (USWC), Air Warfare Commander (AWC), Information Warfare Commander (IWC), Strike Warfare Commander (STWC), and Mine Warfare Commander (MIWC) The concept is based on the premise that the fleet is communicating freely with little or no risk. NDP-6 does not address a concept for tactical command and control of a ship/SAG operating in EMCON as might be the case early in a conflict involving a near peer adversary.
c) Navy Organizational Impediments to Integration. The Navy is not organized to achieve the integration of nonorganic, near real-time, offboard genser or cryptologic sensor information with force organic sensor information. Within OPNAV, the N-8, NAVSEA, PEO Ships and PEO IWS are responsible for surface ship combat systems concepts, requirements, resource sponsorship and designs that to date have been focused exclusively on the integration of ownship and force organic sensor information. Cryptologic and intelligence concepts, requirements, designs and resource sponsorship are the province of the N2/N6, SPAWAR, and PEO C4I. Organizational equities are jealously protected at all levels effectively impeding/preventing consideration of concepts, requirements, funding and development of systems for the integration of organic and offboard tactical information.
In summary, the objectives in this article are sound; but, strategies and command and control concepts are incomplete; and responsibility for integration concepts, requirements, resource sponsorship, and development is fragmented.
The integration of organic and offboard information is feasible at low technical risk and low cost, providing the potential for high returns in distributed lethality combat effectiveness. SECNAV/OPNAV intervention will be needed to bridge this historical gap and achieve these very legitimate information integration objectives.
Thanks for the feedback. Agree with you on all points.
v/r
Chuck