By Jeff Wong
Introduction
Jump into the time machine and fast forward a few years into the future. The United States is at war, things are not going well, and the brass wants to try something new. John McCarthy,1 a Marine lieutenant colonel whose knowledge of technology is limited to the Microsoft Office applications on his molasses-slow government laptop, mulls over his tasks, as specified by his two-star boss, the commander of Joint Task Force 58:
1. Convene a joint planning group to develop a plan for the upcoming counteroffensive. (Check.)
2. Leverage representatives from every staff section and subject-matter experts participating virtually from headquarters in Hawaii or CONUS. (Roger.)
3. Use an experimental machine-learning application to support the planning and execution of the operation. (We’re screwed.)
Nearly 7,000 miles from a home he might never see again, McCarthy considered two aphorisms. The first was from Marcus Aurelius, the second-century Roman emperor and stoic thinker: “Never let the future disturb you. You will meet it, if you have to, with the same weapons of reason which today arm you against the present.” 2 The second was from Mike Tyson, the fearsome boxer, convicted felon, and unlikely philosopher: “Everybody has a plan until they get punched in the mouth.”3
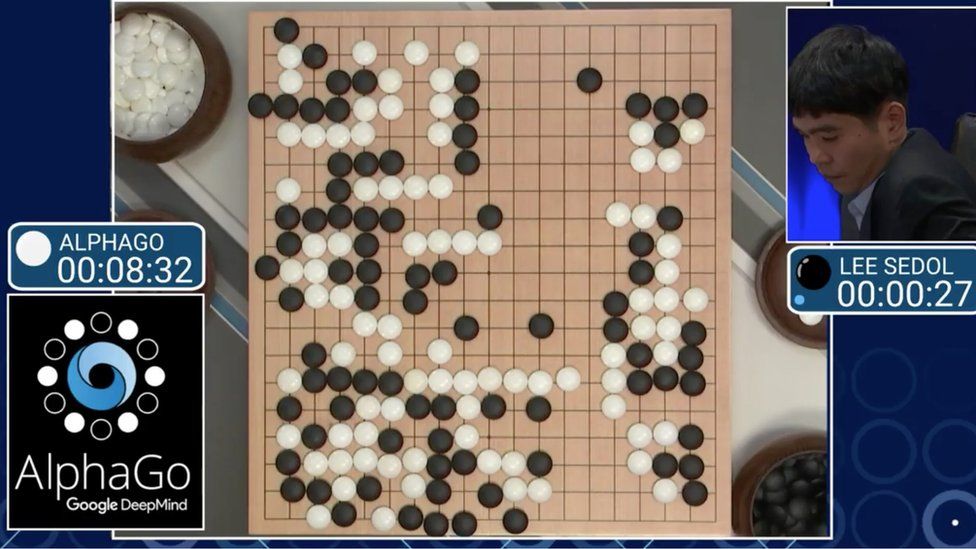
Artificial intelligence (AI), including large-language models (LLMs) such as ChatGPT, is driving a societal revolution that will impact all aspects of life, including how nations wage war and secure their economic prosperity. “The ability to innovate faster and better – the foundation on which military, economic, and cultural power now rest – will determine the outcome of great-power competition between the United States and China,” notes Eric Schmidt, the former chief executive officer of Google and chair of the Special Competitive Studies Project.4 The branch of AI that uses neural networks to mimic human cognition — machine learning (ML) — offers military planners a powerful tool for planning and executing missions with greater accuracy, flexibility, and speed. Senior political and military leaders in China share this view and have made global technological supremacy a national imperative.5
Through analyzing vast amounts of data and applying complex algorithms, ML can enhance situational awareness, anticipate threats, optimize resources, and adapt to generate more successful outcomes. However, as ML becomes more widespread and drives technological competition against China, American military thinkers must develop frameworks to address the role of human judgment and accountability in decision-making and the potential risks and unintended consequences of relying on automated systems in war.
To illustrate the promise and pitfalls of using ML to support decision-making in combat, imagine the pages of a wall calendar flying to some point when America must fight a war against a peer adversary. Taking center stage in this fictional journey are two figures: The first is McCarthy, an officer of average intelligence who only graduated from the Eisenhower School for National Security and Resource Strategy thanks to a miraculous string of B+ papers at the end of the academic year. The second is “MaL,” a multimodal, LLM that is arguably the most capable – yet most immature – member of McCarthy’s planning team. This four-act drama explores how McCarthy and his staff scope the problems they want MaL to help them solve, how they leverage ML to support operational planning, and how they use MaL to support decision-making during execution. The final act concludes by offering recommendations for doctrine, training and education, and leadership and policies to better harness this capability in the wars to come.
Act One: “What Problems Do We Want This Thing to Solve?”
The task force was previously known as “JTF-X,” an experimental formation that blended conventional legacy platforms with AI and autonomous capabilities. As the tides of war turned against the United States and its allies, the Secretary of Defense (SecDef) pressured senior commanders to expand the use of AI-enabled experimental capabilities. Rather than distribute its capabilities across the rest of the joint force, the SecDef ordered JTF-X into duty as a single unit to serve as the theater reserve for a geographic combatant commander. “Necessity breeds innovation… sometimes kicking and screaming,” she said.
Aboard the JTF command ship in a cramped room full of maps, satellite imagery, and charts thick with unit designators, McCarthy stared at a blinking cursor on a big-screen projection of MaL. Other members of his OPT looked over his shoulder as he impulsively typed out, “Alexa, write my OpOrd.” Undulating dots suggested MaL was formulating a response before MaL responded, “I’m not sure what you’re asking for.”
The JPG chief, an Air Force senior master sergeant, voiced what the humans in the room were thinking: “Sir, what problems do we want this thing to solve?”
The incredible capacity of ML tools to absorb, organize, and generate insights from large volumes of data suggests that they hold great promise to support operational planning. Still, leaders, planners, and ML tool developers must determine how best to harness the capability to solve defined military problems. For instance, the Ukrainian military uses AI to collect and assess intelligence, surveillance, and reconnaissance (ISR) data from numerous sources in the Russia-Ukraine conflict.6 But as Ukrainian planners are probably discovering today, they must do more than throw current ML tools at problem sets. Current LLMs fall short of desired capabilities to help human planners infer and make sense within the operating environment. Military professionals must tailor the problem sets to match the capabilities and limitations of the ML solutions.
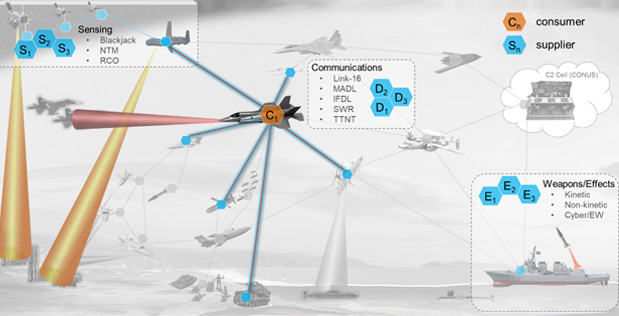
Although tools supporting decision advantage comprised a small fraction of the 685 AI-related projects and accounts within the DoD as of 2021, existing efforts align with critical functions such as the collection and fusion of data from multiple domains (akin to the DoD’s vision for Joint All-Domain Command and Control (JADC2)); multidomain decision support for a combatant command headquarters; automated analysis of signals across the electromagnetic spectrum; and location of bots to support defensive cyber operations.7 There are numerous tools with various tasks and functions, but the crux of the problem will be focusing the right tool or set of tools on the appropriate problem sets. Users need to frame planning tasks and precisely define the desired outputs for a more immature LLM capability, such as the fictional MaL.
McCarthy mapped out a task organization for the JPG to align deliverables with available expertise. The team chief scribbled dates and times for upcoming deliverables on a whiteboard, including the confirmation brief for the commander in 24 hours. An Army corporal sat before a desktop computer to serve as the group’s primary interface with MaL. To help the group develop useful queries and troubleshoot, MaL’s developers in Hawaii participated via a secure video teleconference.
MaL was already able to access volumes of existing data – operations and contingency plans, planning artifacts from previous operations, ISR data from sensors ranging from national assets to stand-in forces in theater, fragmentary orders, and mountains of open-source information.
Act Two: MaL Gets Busy to the ‘Left of the Bang’
Some observers believe that ML capabilities can flatten the “orient” and “decide” steps of the late military theorist John Boyd’s observe-orient-decide-act decision (OODA) loop, expanding a commander’s opportunity to understand context, gain an appreciation of the battlespace, frame courses of action, and explore branches and sequels to inform decisions.8 Nevertheless, the greater capacity that ML tools provide does not eliminate the need for leaders to remain intimately involved in the planning process and work with the platform to define decision points as they weigh options, opportunities, risks, and possible outcomes.
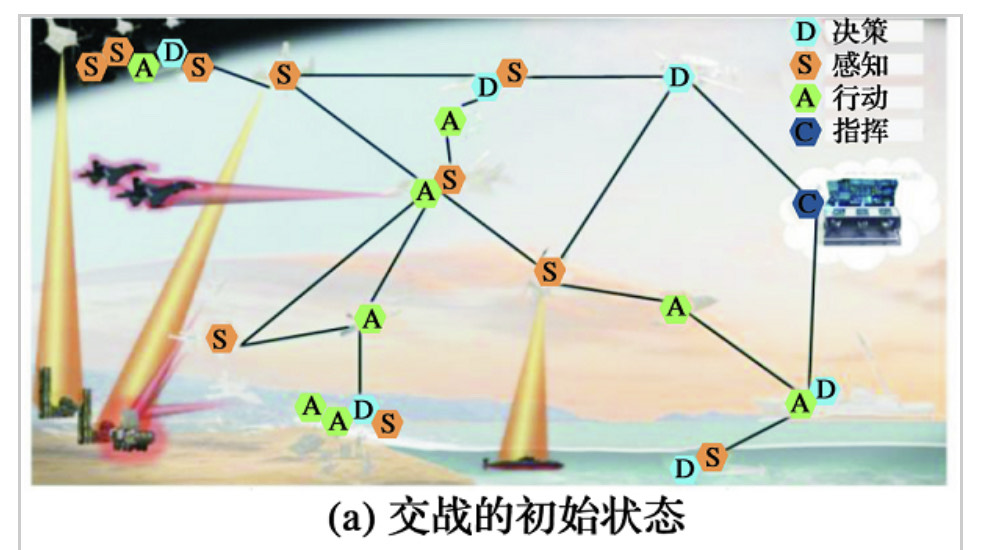
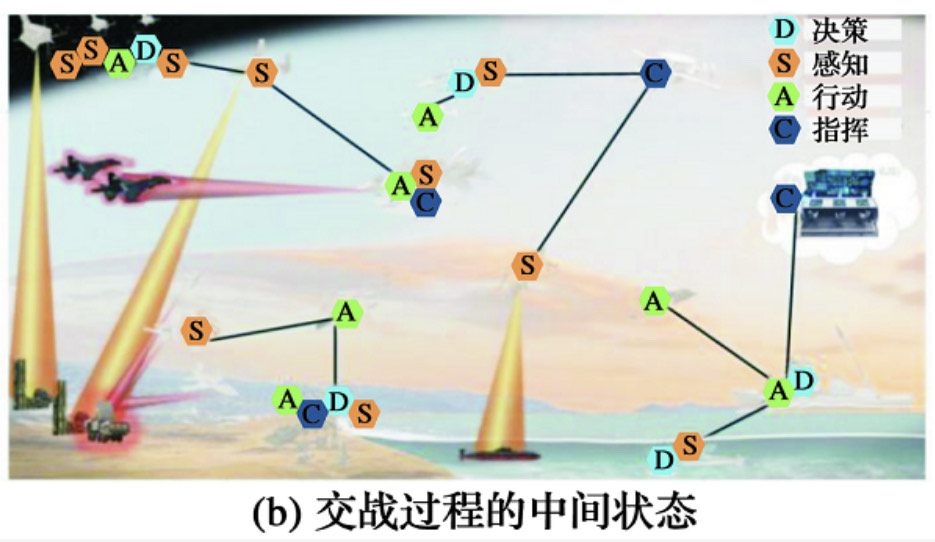
Planners should examine frameworks such as the OODA Loop, IPB, and the Joint Operational Planning Process (JOPP) to guide where they could apply ML to maximum effect. To support IPB, ML can automate aspects of collection and processing, such as identifying objects, selecting potential targets for collection, and guiding sensors. ML capabilities for image and audio classification and natural language processing are already in commercial use. They support essential functions for autonomous vehicles, language translation, and transit scheduling. These commercial examples mirror military use cases, as nascent platforms fuse disparate data from multiple sources in all five warfighting domains.9
MaL’s digital library included the most relevant intelligence reports; adversary tactics, techniques, and procedures summaries; videos of possible target locations taken by uncrewed systems; raw signals intelligence; and assessments of the enemy orders of battle and operational tendencies from the early months of the conflict. The corpus of data also included online news stories and social media postings scraped by an all-source intelligence aggregator.
McCarthy said, “As a first step, let’s have MaL paint the picture for us based on the theater-level operational context, then create an intelligence preparation of the battlespace presentation with no more than 25 PowerPoint slides.” After the clerk entered the query, the graphic of a human hand drumming its fingers on a table appeared.
Two minutes later, MaL saved a PowerPoint file on the computer’s desktop and announced in a metallic voice, “Done, sir, done!” McCarthy and his J-2 reviewed the IPB brief, which precisely assessed the enemy, terrain, weather, and civil considerations. MaL detailed the enemy’s most likely and dangerous courses of action, discussed adversary capabilities and limitations across all domains, and provided a target-value analysis aligning with the most recent intelligence. The J-2 reviewed the product and said, “Not bad.” She added, “Should I worry about losing my job?”
“Maybe I should worry about losing mine,” McCarthy said. “Let’s go through the planning process with MaL and have it generate three COAs based on the commander’s planning guidance and intent statement.”
American military planning frameworks – JOPP and its nearly identical counterparts across the services – are systematic processes that detail the operational environment, the higher commander’s intent, specified and implied tasks, friendly and enemy COAs, and estimates of supportability across all warfighting functions. They benefit the joint force by establishing uniform expectations about the information needed to support a commander’s estimate of the situation. However, current planning frameworks may hinder decision-making because a commander and his staff may become too focused on the process instead of devoting their energies and mental bandwidth to quickly orienting themselves to a situation and making decisions. Milan Vego, a professor of operational art at the U.S. Naval War College, writes of “a great temptation to steadily expand scope and the amount of information in the (commander’s) estimate. All this could be avoided if commanders and staffs are focused on the mental process and making a quick and good decision.”10
An ML-enabled decision-support capability could help planners stay above process minutiae by suggesting options for matching available weapon systems to targets, generating COAs informed by real-time data, and assessing the likelihood of success for various options in a contemporary battlespace, which features space and cyberspace as contested warfighting domains.11
MaL developed three unacceptable COAs which variously exceeded the unit’s authorities as outlined in the JTF’s initiating directive or extended kinetic operations into the adversary’s mainland, risking escalation.
McCarthy rubbed his face and said, “Time for a reboot. Let’s better define constraints and restraints, contain operations in our joint operational area, and have it develop assessments for risks to mission and force.” He added, “And this time, we’ll try not to provoke a nuclear apocalypse.”
The planning team spent several more hours refining their thoughts, submitting prompts, and reviewing the results. Eventually, MaL generated three COAs that were feasible, acceptable, complete, and supportable. MaL tailored battlespace architecture, fire support coordination measures, and a detailed sustainment plan for each COA and mapped critical decision points throughout the operation. MaL also assisted the JTF air officer develop three distinct aviation support plans for each COA.
The planning team worked with MaL to develop staff estimates for each COA. The logistics and communications representatives were surprised at how quickly MaL produced coherent staff estimates following a few hours of queries. The fires, intelligence, and maneuver representatives similarly worked with MaL to develop initial fire support plans to synchronize with the group’s recommended COA.
McCarthy marveled at MaL’s ability to make sense of large amounts of data, but he was also surprised at the ML platform’s tendency to misinterpret words. For instance, it continually conflated the words “delay,” “disrupt,” and “destroy,” which were distinct tactical tasks with different effects on enemy formations. The planning team reviewed MaL’s COA overviews and edited the platform’s work. The staff estimates were detailed, and insightful, but still required corrections.
During the confirmation brief, the JTF commander debated several details about MaL’s outputs and risk assessments of the planning team’s recommended COA. McCarthy said, “Respectfully, Admiral, this is your call. MaL is one tool in your toolbox. We can tweak the COA to suit your desires. We can also calibrate the level of automation in the kill chain based on your intent.”
After a moment, the admiral said, “I’ll follow the planning team’s recommendation. Notice that I didn’t say MaL’s recommendation because MaL is just one part of your team.”
Act Three: MaL Lends a Hand to the Right of the ‘Bang’
Contemporary military thinkers believe that ML-enabled tools could improve decision-making during the execution of an operation, leveraging better situational awareness to suggest more effective solutions for problems that emerge in a dynamic battlespace. However, critics argue that developing even a nascent ML-enabled capability is impossible because of the inherent limits of ML-enabled platforms to generate human-like reasoning and infer wisdom from incomplete masses of unstructured data emanating from a 21st-century battlefield. Some are also concerned about the joint force’s ability to send and receive data from a secure cloud subject to possible malicious cyber activities or adversarial ML. Prussian military thinker Carl von Clausewitz reminds practitioners of the operational art that “War is the realm of uncertainty; three-quarters of the factors on which action in war is based are wrapped in a fog of greater or lesser uncertainty.”12 Technological solutions such as ML-enabled capabilities can temporarily lift parts of this fog for defined periods. Still, users must understand the best use of these capabilities and be wary of inferring certainty from their outputs.
Emerging capabilities suggest that ML can augment and assist human decision-making in several ways. First, ML systems can enhance situational awareness by establishing and maintaining a real-time common operational picture derived from multiple sensors in multiple domains. Greater battlespace awareness provides context to support better decision-making by commanders and more accurate assessments of events on the battlefield. Second, ML can improve the effectiveness and efficiency of kill-chain analytics by quickly matching available sensors and shooters with high-value or high-payoff targets.13 This efficiency is essential in the contemporary battlespace, where ubiquitous sensors can quickly detect a target based on a unit’s emissions in the electromagnetic spectrum or signatures from previously innocuous activities like an Instagram post or a unit’s financial transaction with a host-nation civilian contractor.
Indeed, some AI observers in the U.S. defense analytic community argue that warfighters must quickly adopt ML to maintain a competitive edge against the People’s Liberation Army, which some observers believe will favor the possible gains in warfighting effectiveness and efficiency over concerns about ethical issues such as implementing human-off-the-loop AI strategies.14 ML-enabled feedback constructs will enhance the control aspects of command and control to employ a large, adaptable, and complex multidomain force.15
It was now D+21. JTF-58 achieved its primary objectives, but the campaign did not unfold as intended. During the shaping phase of the operation, several high-value targets, including mobile anti-ship cruise missile batteries, escaped kinetic targeting efforts, living to fight another day and putting U.S. naval shipping at risk for the latter phases of the campaign. MaL failed to update the developers’ advertised “dynamic operating picture” despite attempts by forward-deployed sensors and reconnaissance teams to report their movement. Incredibly, the DoD still did not have access to data from some weapon systems due to manufacturer stipulations.16
MaL’s developers insisted that the forward-deployed sensors should have had enough computing power to push edge data to the JTF’s secure cloud. The CommO speculated that environmental conditions or adversary jamming could have affected connectivity. McCarthy shook his head and said, “We need to do better.”
MaL performed predictably well in some areas to the right of the bang. The task force commander approved using MaL to run networked force protection systems, including a Patriot battery that successfully intercepted an inbound missile and electronic-warfare (EW) systems that neutralized small unmanned aerial systems targeting a fuel farm. MaL’s use in these scenarios did not stretch anyone’s comfort level since these employment methods were barely different than the automation of systems like the U.S. Navy’s Phalanx close-in weapon system (CIWS), which has detected, evaluated, tracked, engaged, and conducted kill assessments of airborne threats for more than four decades.17
MaL’s communications and logistics staff estimates were precise and valuable for the staff. The CommO adjusted the tactical communications architecture based on MaL’s predictions about enemy EW methods and the effects of weather and terrain on forward maneuver elements. Similarly, the LogO worked with the OpsO to establish additional forward-arming and refueling points (FARPs) based on MaL’s fuel and munitions consumption projections.
In the middle of the operation, the task force commander issued a fragmentary order to take advantage of an unfolding opportunity. MaL leveraged open-source data from host-nation news websites and social media postings by enemy soldiers to inform battle damage assessment of kinetic strikes. Some of that information was fake and skewed the assessment until the intelligence officer corrected it by comparing it with satellite imagery and human intelligence reporting.
As with any emerging capability, commanders and their staffs must consider the risks of integrating ML into the planning, execution, and assessment of operations. One of the risks is inherent in forecasting, as the ML platform artificially closes the feedback loop to a decision-maker sooner than one would expect during real-world operations. Retired U.S. Navy Captain Adam Aycock and Naval War College professor William Glenney IV assert that this lag might make ML outputs moot when a commander makes a decision. “The operational commander might not receive feedback, and the effects of one move might not be recognized until several subsequent moves have been made,” Aycock and Glenney write. “Furthermore, a competent enemy would likely attempt to mask or manipulate this feedback. Under such circumstances … it is difficult to ‘learn’ from a first move in order to craft the second.”18
Another risk is that the data used by ML platforms are, in some way, inaccurate, incomplete, or unstructured. Whether real or training, flawed data will lead to inaccurate outputs and likely foul an ML-enabled tool’s assessment of the environment and COA development. “Unintentional failure modes can result from training data that do not represent the full range of conditions or inputs that a system will face in deployment,” write Wyatt Hoffman and Heeu Millie Kim, researchers with the Center for Security and Emerging Technology at Georgetown University. “The environment can change in ways that cause the data used by the model during deployment to differ substantially from the data used to train the model.”19
The corollary to inaccurate data is adversarial ML, in which an enemy manipulates data to trick an ML system, degrade or disrupt optimal performance, and erode users’ trust in the capability. Adversarial ML tricks can trick an ML model into misidentifying potential targets or mischaracterizing terrain and weather. In one notable demonstration of adversarial ML, researchers at the Chinese technology giant Tencent placed stickers on a road to trick the lane recognition system of a Tesla semi-autonomous car, causing it to swerve into the wrong lane.20 Just the possibility of a so-called “hidden failure mode” could exacerbate fears about the reliability of any ML-enabled system. “Operators and military commanders need to trust that ML systems will operate reliably under the realistic conditions of a conflict,” Hoffman and Kim write. “Ideally, this will militate against a rush to deploy untested systems. However, developers, testers, policymakers, and commanders within and between countries may have very different risk tolerances and understandings of trust in AI.”21
Act Four: Hotwash
McCarthy took advantage of an operational pause to conduct a hotwash. Over lukewarm coffee and Monsters, the conversation gravitated toward how they could use MaL better. The group scribbled a few recommendations concerning integrating ML into doctrine, training and education, and leadership and policies until the ship’s 1-MC sounds general quarters.
Doctrine: To realize the utility of ML, military leaders should consider two changes to existing doctrine. First, doctrine developers and the operational community should consider the concept of “human command, machine control,” in which ML would use an auction-bid process akin to ride-hailing applications to advertise and fulfill operational requirements across the warfighting functions. Under this construct, a commander publishes or broadcasts tasks, including constraints, priorities, metrics, and objectives. “A distributed ML-enabled control system would award-winning bids to a force package that could execute the tasking and direct the relevant forces to initiate the operation,” write naval theorists Harrison Schramm and Bryan Clark. “Forces or platforms that accept the commander’s bid conducts (or attempts to conduct) the mission and reports the results “when communications availability allows.”22 This concept supports mission-type orders/mission command and allows C2 architectures to flex to instances and areas subject to low-bandwidth constraints.23
Second, doctrine developers should adjust joint, service, and domain-centric planning processes to account for additional planning aids, such as LLMs, modeling and simulation, and digital twins, which can more deeply explore COAs, branches, and sequels and accelerate understanding of threats and the operating environment. Explicitly changing planning doctrine to account for these emerging capabilities will encourage their use and emphasize their criticality to effective planning.
Training and Education: Tactical units must train and continually develop ML technical experts capable of conducting on-the-spot troubleshooting and maintenance of the tool. Meanwhile, the services should develop curricula to train budding junior leaders — corporals, sergeants, lieutenants, ensigns, and captains — that introduce them to machine-learning tools applicable to their warfighting domains, provide best principles for generating productive outputs, and articulate risks – and risk mitigations – due to skewed data and poor problem framing.
Best practices should also be documented and shared across the DoD. Use of ML capabilities should become part of a JPG’s battle drill, featuring a designated individual whose primary duty is to serve as the human interface with a decision-support tool such as MaL. Rather than work from scratch at the start of every planning effort, JPGs should have a list of queries readily available for a range of scenarios that can inform a commander’s estimate of the situation and subsequent planning guidance, and formulation of intent based on an initial understanding of the operating environment. Prompts that solicit ML-enabled recommendations on task organization, force composition and disposition, risks to force or mission, targeting, and other essential decisions should be ready for immediate use to speed the JPG’s planning tempo and, ultimately, a unit’s speed of action as well. The information management officer (IMO), which in some headquarters staffs is relegated to updating SharePoint portals, should be the staff’s subject matter expert for managing ML capabilities. IMOs would be the military equivalent of prompt engineers to coax and guide AI/ML models to generate relevant, coherent, and consistent outputs to support the unit’s mission.24
Leadership and Policies: There are implications for senior leaders for warfighting and policy. Within a warfighting context, senior defense leaders must identify, debate, and develop frameworks for how commanders might use ML to support decision-making in wartime scenarios. It seems intuitive to use a multimodal LLM tool such as the fictitious MaL to support IPB, targeting, and kill chain actions; in the same way, campaign models are used to inform combatant commander planning for crises and contingencies.
However, leaders and their staffs must also understand the limitations of such tools to support a commander’s decision-making. “Do not ask for an AI-enabled solution without first deciding what decision it will influence and what the ‘left and right limits’ of the decision will be,” Schramm and Clark warn.25 Likewise, AI might not be the appropriate tool to solve all tactical and operational problems. “Large data-centric web merchants such as Amazon are very good at drawing inferences on what people may be interested in purchasing on a given evening because they have a functionally infinite sample space of previous actions upon which to build the model,” they write. “This is radically different from military problems where the amount of data on previous interactions is extremely small and the adversary might have tactics and systems that have not been observed previously. Making inference where there is little to no data is the domain of natural intelligence.”26
Meanwhile, future acquisition arrangements with defense contractors must provide the DoD with data rights – particularly data generated by purchased weapon systems and sensors – to optimize the potential of ML architecture in a warfighting environment.27 Such a change would require the DoD to work with firms in the defense industrial base to adjudicate disagreements over the right to use, licensing, and ownership of data – each of which might bear different costs to a purchaser.
Epilogue
Technologists and policy wonks constantly remind the defense community that the Department must “fail fast” to mature emerging technologies and integrate them into the joint force as quickly as possible. The same principle should guide the development of AI/ML-enabled warfighting solutions. Commanders and their staffs must understand that this is a capable tool that, if used wisely, can significantly enhance the joint force’s ability to absorb data from disparate sources, make sense of that information, and close kill chains based on an ML tool’s assessment.
If used unwisely, without a solid understanding of what decisions ML will support, the joint force may be playing a rigged game against a peer adversary. ML-enabled capabilities can absorb large amounts of data, process and organize it, and generate insights for humans who work at a relative snail’s pace. However, these nascent tools cannot reason and interpret words or events as a competent military professional can. As strategic competition between the United States and China intensifies over Taiwan, the South China Sea, the Russian-Ukraine war, and other geopolitical issues, American political and military leaders must develop a better understanding of when and how to use ML to support joint force planning, execution, and assessment in combat, lest U.S. service members pay an ungodly sum of the butcher’s bill.
Lieutenant Colonel Jeff Wong, a U.S. Marine Corps reserve infantry officer, studied artificial intelligence at the Eisenhower School for National Security and Resource Strategy, National Defense University in the 2022-2023 academic year. In his civilian work, he plans wargames and exercises for various clients across the Department of Defense.
The views expressed in this paper are those of the author and do not necessarily reflect the official policy or position of the National Defense University, the Department of Defense, or the U.S. Government.
References
1. The fictional hero of this story, John McCarthy, is named after the Massachusetts Institute of Technology researcher who first coined the term “artificial intelligence.” Gil Press, “A Very Short History of Artificial Intelligence,” Forbes, December 30, 2016, https://www.forbes.com/sites/gilpress/2016/12/30/a-very-short-history-of-artificial-intelligence-ai/?sh=51ea3d156fba.
2. Marcus Aurelius, Meditations, audiobook.
3. Mike Berardino, “Mike Tyson Explains One of His Most Famous Quotes,” South Florida Sun-Sentinel, November 9, 2012, https://www.sun-sentinel.com/sports/fl-xpm-2012-11-09-sfl-mike-tyson-explains-one-of-his-most-famous-quotes-20121109-story.html.
4. Eric Schmidt, “Innovation Power: Why Technology Will Define the Future of Geopolitics,” Foreign Affairs, March/April 2023.
5. “Military-Civil Fusion and the People’s Republic of China,” U.S. Department of State, May 2020.
6. Eric Schmidt, “Innovation Power: Why Technology Will Define the Future of Geopolitics,” Foreign Affairs, March/April 2023.
7. Wyatt Hoffman and Heeu Millie Kim, “Reducing the Risks of Artificial Intelligence for Military Decision Advantage,” Center for Security and Emerging Technology Policy Paper (Washington, D.C.: Georgetown University, March 2023), 12.
8. James Johnson, “Automating the OODA Loop in the Age of AI,” Center for Strategic and International Studies, July 25, 2022, https://nuclearnetwork.csis.org/automating-the-ooda-loop-in-the-age-of-ai/.
9. Hoffman and Kim, “Reducing the Risks of Artificial Intelligence for Military Decision Advantage,” 7.
10. Milan Vego, “The Bureaucratization of the U.S. Military Decision-making Process,” Joint Force Quarterly 88, January 9, 2018, https://ndupress.ndu.edu/Publications/Article/1411771/the-bureaucratization-of-the-us-military-decisionmaking-process/.
12. Carl von Clausewitz, On War, ed. and trans. Michael Howard and Peter Paret (Princeton: Princeton University Press, 1976), 101.
14. Elsa Kania, “AI Weapons” in China’s Military Innovation, Brookings Institution, April 2020.
15. Harrison Schramm and Bryan Clark, “Artificial Intelligence and Future Force Design,” in AI at War (Annapolis, Md.: Naval Institute Press, 2021), 240-241.
16. Josh Lospinoso, Testimony on the State of Artificial Intelligence and Machine Learning Applications to Improve Department of Defense Operations before the Subcommittee on Cybersecurity, U.S. Senate Armed Services Committee, April 19, 2023, https://www.armed-services.senate.gov/hearings/to-receive-testimony-on-the-state-of-artificial-intelligence-and-machine-learning-applications-to-improve-department-of-defense-operations. “Today, the Department of Defense does not have anywhere near sufficient access to weapon system data. We do not – and in some cases, due to contractual obligations, the Department cannot — extract this data that feeds and enables the AI capabilities we will need to maintain our competitive edge.”
17. MK15 – Phalanx Close-In Weapon System (CIWS), U.S. Navy, September 20, 2021, https://www.navy.mil/resources/fact-files/display-factfiles/article/2167831/mk-15-phalanx-close-in-weapon-system-ciws/.
18. Adam Aycock and William Glenney IV, “Trying to Put Mahan in a Box,” in AI at War, 269-270.
19. Hoffman and Kim, CSET Policy Brief, 8.
20. Ibid, 8-9.
22. Schramm and Clark, “Artificial Intelligence and Future Force Design,” 239-241.
23. AI at War, 241.
24. Craig S. Smith, “Mom, Dad, I Want To Be A Prompt Engineer,” Forbes, April 5, 2023, https://www.forbes.com/sites/craigsmith/2023/04/05/mom-dad-i-want-to-be-a-prompt-engineer/amp/.
26. AI at War, 248.
27. Heidi M. Peters, “Intellectual Property and Technical Data in DoD Acquisitions,” Congressional Research Service In-Focus, IF12083, April 22, 2022, https://crsreports.congress.gov/product/pdf/IF/IF12083.
Featured Image: PHILIPPINE SEA (Sept. 22, 2020) Cpl. Clayton A. Phillips, a network administrator with Marine Air Control Group 18 Detachment, 31st Marine Expeditionary Unit (MEU), and a native of Beech Bluff, Tennessee, tests the connectivity of the Networking On-the-Move Airborne (NOTM-A) communications system during flight operations from the amphibious assault ship, USS America (LHA 6). (U.S. Marine Corps photo by Lance Cpl. Brienna Tuck)